What is DMZ Network?
In computer security, a DMZ stands for a demilitarized zone and is also known as perimeter network, or screened subnet. Let’s take a look at the topics that we will be covering in this blog today.
- What is DMZ Network?
- Purpose of a DMZ
- Why are DMZ Networks Important?
- How does a DMZ work?
- Architecture and Design of DMZ Networks
- Benefits of Using a DMZ
- Applications of DMZ
- Key Takeaways
A DMZ configuration allows for additional security to protect against external attacks in a Local Area Network (LAN). The term, ‘DMZ’, has been borrowed from the geographic buffer zone that was set up at the end of the Korean War between North Korea and South Korea. But, what is DMZ network in computer security?
What is a DMZ Network?
A DMZ is a physical or logical subnet that isolates a LAN from untrusted networks like the public internet. Any service that is offered to users on the public internet should be set up in the DMZ network. The external-facing servers, services, and resources are usually placed there. Services include web, Domain Name System (DNS), email, proxy servers and File Transfer Protocol (FTP), Voice over Internet Protocol (VoIP).
The resources and servers in the DMZ network can be accessed from the internet but are isolated with very limited access to the LAN. Due to this approach, the LAN has an additional layer of security restricting a hacker from directly accessing the internal servers and data from the internet.
Hackers and cyber criminals can reach the systems that run services on a DMZ server. The security on those servers must be tightened to be able to withstand constant attacks.
The main objective of a DMZ is to enable organizations to use the public internet while ensuring the security of their private networks or LANs.
Purpose of a DMZ
The DMZ network is there to protect the hosts that have the most vulnerabilities. DMZ hosts mostly involve services that extend to the users that are outside of the local area network. The increased potential for attacks makes it necessary for them to be placed into the monitored subnetwork. This will protect the rest of the network if they end up getting compromised.
Hosts in the DMZ have access permissions to other services within the internal network and this access is tightly controlled due to the fact that the data that is passed through the DMZ is not as secure.
To help expand the protected border zone, the communications between the DMZ hosts and the external network are restricted. This enables the hosts in the protected network to communicate with the internal and external network, while the firewall takes care of the separation and management of all the traffic that is shared between the DMZ and the internal network.
Enroll in our Ethical Hacking course now to learn various Ethical Hacking concepts.
An additional firewall typically protects the DMZ from exposure to everything on the external network. Here are some uses of DMZ in some of the most common services accessible to users on communicating from an external network:
- Web Servers – Web servers that maintain communication with an internal database server may need to be placed into a DMZ for the safety of the internal database, which often stores sensitive information. The web servers can then interact through an application firewall or directly with the internal database server, while still having DMZ protections.
- Mail Servers – Emails and user databases that contain personal messages and login credentials are usually stored on servers that do not have direct access to the internet. An email server can be built or set up inside the DMZ for interaction with and access to the email database without exposing it to potentially harmful traffic.
- FTP Servers: FTP servers can host critical content on the website of an organization, and allow direct interaction with files. Due to this, FTP servers should always be partially isolated from the internal systems that are critical.
The additional security provided from external attacks by a DMZ configuration typically has no use against internal attacks like spoofing via email or other means or sniffing communication via a packet analyzer.
For almost as long as firewalls have existed, DMZ networks have been an integral part of enterprise network security. DMZ networks are deployed to protect sensitive systems and resources. DMZ networks are often used for:
- Isolating and separating potential target systems from internal networks
- Reducing and controlling access to the systems by external users
- Hosting corporate resources to give authorized access to some of these resources to external users
Enterprises have lately chosen to use virtual machines or containers to isolate a few sections of the network or specific applications from the rest of the corporate environment. Cloud technologies have eliminated the need for in-house web servers in organizations. Most external-facing infrastructures that were once set up in the enterprise DMZ have moved to the cloud (for example, SaaS apps).
Check out this Cyber Security Course offered by Intellipaat.
Why are DMZ Networks Important?
Internet-enabled devices on many home networks are built around LAN, which accesses the internet from a broadband router. The router acts as both a connection point and a firewall that automates traffic filtering to ensure that the messages that enter the LAN are safe.
A DMZ on a home network can be built by adding a dedicated firewall between the router and the LAN. While this structure can be expensive, it can effectively protect internal devices from sophisticated attacks and possible external attacks.
DMZs are crucial for network security for both individual users and large organizations. The extra layer of security tightly protects the computer network by restricting remote access to internal servers and data, which when breached can be very damaging.
How does a DMZ work?
Customers of a business that has a public website must make their web server accessible from the internet to visit the website. This puts their entire internal network at high risk. To avoid this, the organization can pay a hosting firm for hosting the website or their public servers on a firewall. However, this could end up negatively affecting the performance. Therefore, the public servers are hosted on a separate or isolated network.
The DMZ network serves as a buffer between the internet and the private network of an organization. It is isolated by a security gateway like a firewall that filters traffic between the DMZ and LAN. The default DMZ server is secured by another gateway that filters the incoming traffic from external networks. It is ideally located between two firewalls.
The DMZ firewall setup makes sure that the incoming network packets are observed by a firewall or other security tools before they reach the servers hosted in the DMZ. So, even if an attacker somehow gets past the first firewall, they will have to have access to the hardened services in the DMZ to cause any kind of serious damage to a business.
If the external firewall is penetrated by an attacker and a system in the DMZ is compromised, they will also have to get past an internal firewall before even gaining access to all the sensitive corporate data. A highly skilled attacker may sometimes be able to breach a secure DMZ, but various alarm systems and resources are there to provide plenty of warning about the breach in progress.
Organizations that are required to comply with regulations sometimes install a proxy server in the DMZ. This allows simplification of the monitoring and recording of user activities and the centralization of web content filtering. It also ensures that employees are using the system to gain access to the internet.
Go through this Cyber Security tutorial for beginners and learn the basics of Cyber Security.
Architecture and Design of DMZ Networks
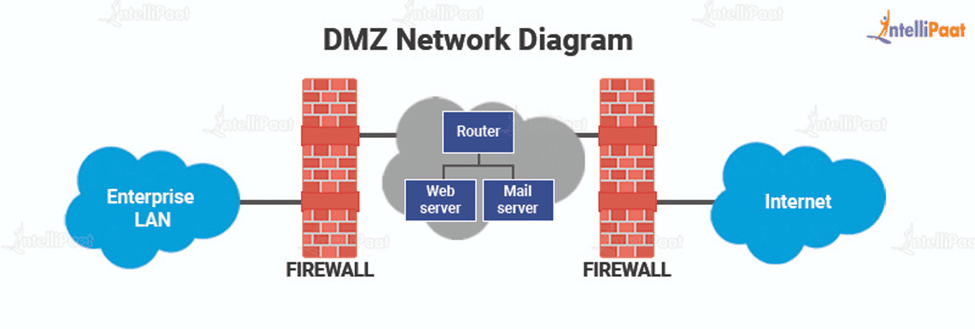
There are several ways a network can be built using a DMZ. The two primary methods of achieving this are a single firewall (or a three-legged model) or dual firewalls. Both these systems can be expanded to build complex DMZ architectures that satisfy network requirements:
- Single Firewall
Using a single firewall with a minimum of 3 network interfaces is a modest approach to network architecture. The DMZ is placed inside this firewall. The connection to the external network device is made from the ISP. The second device connects the internal network and the third network device handles the connections within the DMZ.
- Dual Firewall
Using two firewalls is a more secure method to create a DMZ. The first firewall is referred to as the frontend firewall and is built to only allow traffic that is headed towards the DMZ. The second firewall or the backend firewall is only in charge of the traffic that travels to the internal network from the DMZ.
To further increase the level of protection, firewalls that are built by separate vendors are used as there are fewer possibilities of having the same security vulnerabilities. It is a more effective, but more costly scheme to be implemented across a large network.
Security controls for various network segments can also be fine-tuned by organizations. An Intrusion Detection System (IDS) or Intrusion Prevention System (IPS) within a DMZ can be configured to block any traffic other than Hypertext Transfer Protocol Secure (HTTPS) requests to the Transmission Control Protocol (TCP) port 443.
Want to learn the basics of Ethical Hacking? Go through our Ethical Hacking tutorial for beginners now!
Benefits of Using DMZ
The primary benefit of a DMZ is that it provides an extra layer of advanced security to an internal network by restricting access to sensitive information and servers. It allows the website users to avail themselves of certain services while having a buffer between them and the private network of the organization. The DMZ also offers additional security benefits like:
- Enabling Access Control – Businesses can provide access to services outside the perimeters of their network to their users through the public internet. The DMZ allows this while ensuring network segmentation to make it challenging for unauthorized users to access the private network. There can also be a proxy server included with the DMZ, which centralizes internal traffic flow and simplifies its monitoring and logging.
- Preventing Network Reconnaissance: Providing a buffer between a private network and the internet helps a DMZ prevent attackers from performing reconnaissance work that is carried out to search for potential targets. Servers that are within the DMZ do get exposed to the public but have an extra layer of security by a firewall that prevents anyone from seeing inside the internal network.
If a DMZ system happens to get compromised, the internal firewall will separate the private network from the DMZ and keep it secure making external reconnaissance hard.
- Blocking Internet Protocol (IP) Spoofing: Hackers attempt to gain access to systems by falsifying an IP address and impersonating a device that is already approved and signed in to a network. However, a DMZ is capable of discovering and stalling such attempts as another service verifies the legitimacy of the IP address. The DMZ enables network segmentation to create a space for organized traffic and public services to be accessible away from the internal networks that are private.
Career Transition
Applications of DMZs
Some of the various DMZ network examples can be seen in:
- Cloud Services
Some cloud computing services use a hybrid security approach with an implemented DMZ between an on-premises network of an organization and the virtual network. This is typically applied when an organization’s applications are run partly on the premises and partly on the virtual network.
DMZ is also used where audit is required for outgoing traffic or where granular traffic control is necessary between the virtual network and the on-premises data center.
- Home Networks
A DMZ is also useful in home networks where computers and other devices are connected to the internet through a broadband router and a LAN configuration. Some home routers have a DMZ host feature. This can be contrasted with DMZ subnetworks that are used in organizations with more devices than one would usually find in a home.
One device on the home network is designated by the DMZ host feature to operate outside of the firewall and serve as the DMZ. The rest of the home network is inside the firewall. Sometimes, a gaming console is chosen to be the DMZ host so that gaming is not interrupted by the firewall. The console can also act as a good DMZ host because it usually doesn’t hold sensitive information compared to a personal computer.
- Industrial Control Systems (ICS)
Security risks of ICSs are offered potential solutions by DMZs. Industrial equipment are merged with IT, which makes for smarter and more efficient production environments. However, this also results in a larger threat surface.
Much of the industrial or Operational Technology (OT) equipment connected to the internet are not designed to deal with attacks like IT devices do. A DMZ allows for increased network segmentation that can make it challenging for ransomware and other network threats to fill the gap between the IT systems and their much more susceptible OT counterparts.
Courses you may like
Key Takeaways
A DMZ layer is fundamental in network security. A layered security structure is created by the subnetworks that reduce the chances of facing attacks as well as the severity of it if one happens. They isolate any outward-facing applications from the corporate network. Any system or application facing the public internet should be put in a DMZ.
Make sure to visit our Cyber Security Community and get your questions answered by experts.
The post What is DMZ Network? appeared first on Intellipaat Blog.
Blog: Intellipaat - Blog
Leave a Comment
You must be logged in to post a comment.