Nmap Commands – Complete Tutorial with Cheat Sheet
Let’s discuss Nmap and its interesting commands in detail in this tutorial and look out why it’s the best tool for penetration testing.
Nmap
Network Mapper is referred to as Nmap. A network’s IP addresses and ports can be scanned with this free and open-source Linux command-line tool in order to find installed programs. Network administrators can use Nmap to identify the devices connected to their network, find open ports and services, and find security holes.
The subjects we will cover in this tutorial are listed below:
- What is Nmap?
- History of Nmap
- How does Nmap works?
- Installation of Nmap
- Basic Network Scan of Nmap
- Commands of Nmap
- Use Case of Nmap
- Conclusion
Check out our Youtube Video for Ethical Hacking Course
What is Nmap?
Gordon Lyon created the open-source security auditing and network scanning program known as Nmap or Network Mapper. Its design enables fast analysis of both small-scale networks and individual hosts. It is frequently used by network managers to identify the active devices on a system, the port number to which they are connected, and any open ports that might be in use.
When conducting network penetration testing, Nmap is useful and Nmap may be used on various common operating systems, including Linux, Windows, macOS, and BSD. It is platform-neutral. It is simple to use and has both a graphical user interface (GUI) and a command-line interface (CLI) (GUI).
Hackers can use Nmap to access unrestricted ports on a system. A hacker would only need to run Nmap on the target machine, search for vulnerabilities, and figure out how to exploit them in order to gain access. However, users of the software platform are not limited to hackers. It is frequently used by IT security firms to simulate the kinds of assaults that a system can encounter.
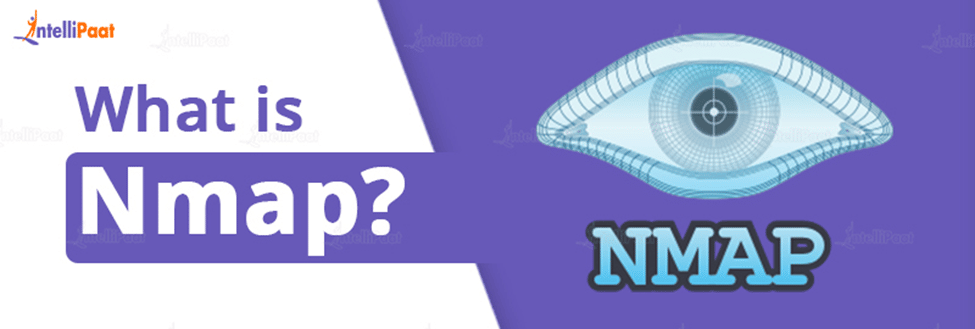
History of Nmap
In terms of technology, NMAP has a somewhat lengthy history, starting in September 1997. It was first published as a 2,000-line article in Issue 51 of the Phrack journal, with a slightly modified version appearing in Issue 52.
The second version, which included more tools, enhancements, and features, was released in December 1998 and included 8,000 lines of code.
NMAP got a GUI in April 1999, however, the majority of users continued to favor the command line. A native Windows version is released in December 2000. NMAP version 3 with support for macOS is released shortly after the author, network security expert Gordon Lyon, leaves Netscape to focus on the project full-time in July 2002.
After appearing in the movie Matrix Reloaded in May 2003, NMAP receives more attention and fame and eventually becomes a common prop in Hollywood hacking movies.
In January 2006, version 4 was made available. This version featured runtime interaction that showed job completion times.
In June 2006, NMAP gains a more precise OS detection. Users can now develop their own scripts to automate a variety of processes thanks to the addition of scripting capabilities in December 2006. A new GUI is added in July 2007, and version 4.5 is launched in December of that same year to celebrate the tool’s tenth birthday.
Version 4.75, which has significant enhancements to scripting, features, the GUI, and OS identification, was released in September 2008. In 2009 NMAP 6 has been made available. NMAP’s current version and used for penetration testing, 7.9, is as of October 2020.
How does Nmap works?
Nmap finds hosts and services on a network by scanning them. When those hosts and services are located, the software platform sends information to them; they then respond. Nmap analyses the returned answer by reading it and using the data to build a network map. The map that is produced provides thorough details on what each port is doing, who (or what) is using it, how hosts are connecting, what gets through the firewall, and what doesn’t, as well as a list of any security risks that may arise.
How is that done, all of it? Nmap makes use of a sophisticated network of scripts that talk to every component of the network. The scripts serve as a means of communication between the network’s human users and its many components. The scripts that Nmap employs are capable of network discovery, vulnerability exploitation, backdoor detection, and vulnerability detection. Although Nmap is a very powerful piece of software, proper use usually necessitates a substantial amount of background knowledge.
Nmap can be used by internet security firms to scan a system and identify any vulnerabilities that a hacker might be able to take advantage of. One of the more popular tools for checking networks for open ports and other vulnerabilities is the open-source, free application. By offering a first-rate web-based security solution that makes sure that the clients’ ports stay safely closed to anyone without permission, Holm Security makes excellent use of this technology.
Are you interested? Check out Intellipaat’s Ethical Hacking Training Certification Course and enroll now!
Installation of Nmap
Nmap installation is simple, although it depends on your operating system. You can download the program’s Windows, Mac, and Linux versions from this page.
- Nmap comes with a unique installer for Windows (nampsetup.exe). This installer can be downloaded and executed to automatically configure Nmap on your computer.
- Nmap has a specific installer for Mac as well. To launch this installer, run the Nmap-pkg file. You could receive a warning that Nmap is an “unidentified developer” on some newer macOS versions, but you can disregard this warning.
- Linux users have the option of using their preferred package manager or compiling Nmap from the source. Run Nmap -version to see if Nmap is installed, then Sudo apt-get install Nmap to install Nmap using apt to install.
Career Transition
Basic Network Scan of Nmap
- Running a Ping Scan
Finding active hosts on your network is one of Nmap’s most fundamental tasks. Nmap performs a ping scan to accomplish this. Without sending any messages to these hosts, this lists every IP address that is active at the moment.
Use this command to perform a host scan:
# 192.100.1.1/24 nmap -sp
A list of hosts on your network and the total number of IP addresses assigned are then returned by this command. You can run additional commands (see below) to look into any hosts or IP addresses on this list that you cannot account for.
- Running a Host Scan
Nmap may be used to do a host scan, which is a more potent method of network scanning. A host scan actively sends ARP request packets to every host connected to your network, in contrast to a ping scan. Each host then replies to this packet with an additional ARP message that includes its MAC address and status.
Use this command to perform a host scan:
Nmap -sp "target IP range"
This provides details on each host, including their MAC address, latency, and any associated descriptions. This may be a potent method for identifying dubious hosts that are linked to your network.
Go through these Ethical Hacking Interview Questions and Answers to excel in your interview.
Commands of Nmap
Now we would like to explain the Commands of Nmap which are as follows:

- OS Scanning
Nmap transmits TCP and UDP packets to a specific port during this type of scan, then examines the response. It uses a database of 2600 operating systems to compare this response, and it then returns details on the OS (and version) of a host.
Utilize the following command to launch an OS scan:
nmap -O "target IP"
- Host Inspection
Host scanning provides additional in-depth data about a specific host or a group of IP addresses. As previously noted, you can run a host scan by using the command:
Nmap -sp "target IP range"
- Port Scanning
Nmap can be used in a variety of ways to conduct port scanning. The following are the most typical:
- TCP SYN scan: #
- TCP connect scan in # sT
- sU UDP scans at #
- SCTP INIT scan # sY
- sN TCP NULL in #
- Ping Scanning
A ping scan, as previously indicated, returns data on each active IP on your network. The command for a ping scan is:
# 192.100.1.1/24 nmap -sp
- Scanning The Most Popular Ports
This command comes in very handy if you have Nmap running on your home server. It automatically looks for a host by scanning a number of the most “popular” ports. The command can be written as:
20 192.168.1.106 nmap —top-ports
Nmap swiftly searches that many ports if the number of ports to scan is substituted for the “20”. It provides a brief output that summarises the state of the most popular ports, allowing you to quickly determine whether any ports are open needlessly.
- Publish to a file
You can add an extension to your commands to output the findings of your Nmap scans to a file. Just add:
output.txt, -oN
Add your order to save the outcomes to a text file, or
output.xml -o to create an XML output.
- Disable DNS Name Resolution
Finally, by turning off reverse DNS resolution with the -n argument, you can speed up Nmap scans. If you want to scan a big network, this can be really helpful. For instance, add -n: to the basic ping scan command to disable DNS resolution.
# 192.100.1.1/24 nmap -sp -n
This Ethical Hacking Tutorial will help you learn Ethical Hacking from scratch.
Use Case of Nmap
- Use Case one
The Nmap syntax is described as follows on the main page:
nmap [...] [Scan Type] [<Options>] the target description
While Nmap has many switch options available, let’s concentrate on the most useful one. Use the nmap hostname> command as follows to scan the hostname for this use case:
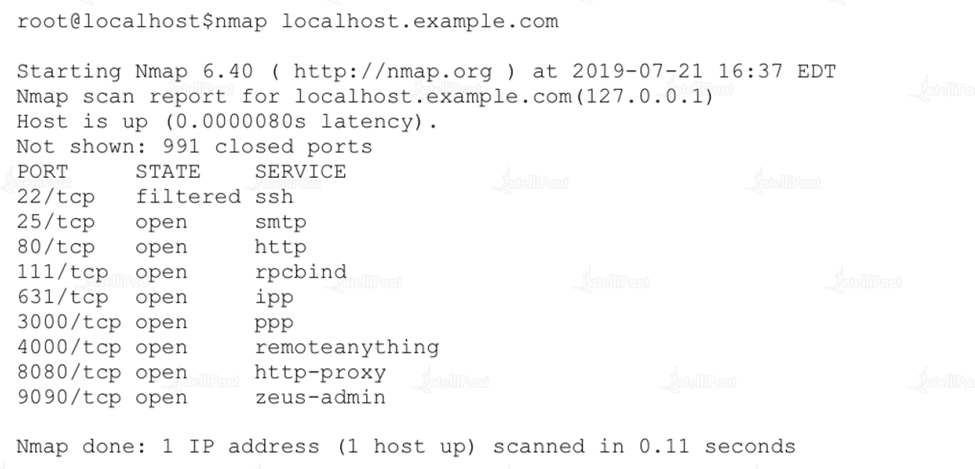
- Use Case Two
List all the hosts in a hosts.txt file if you need to scan more than one host. Utilize the following command: nmap -iL “file containing host names”
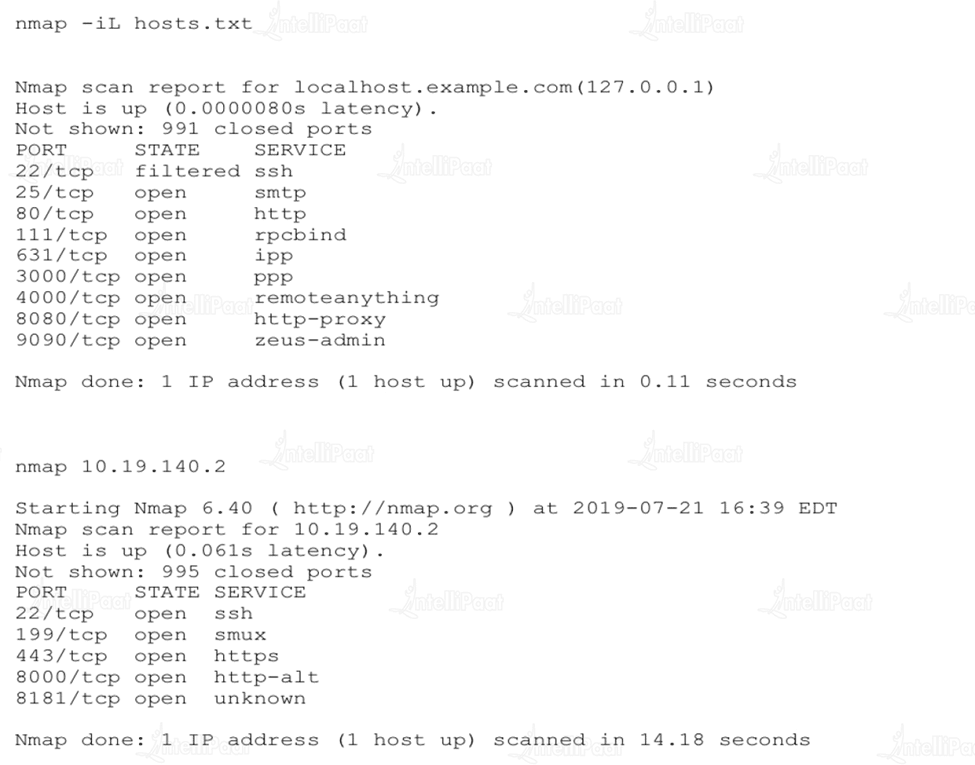
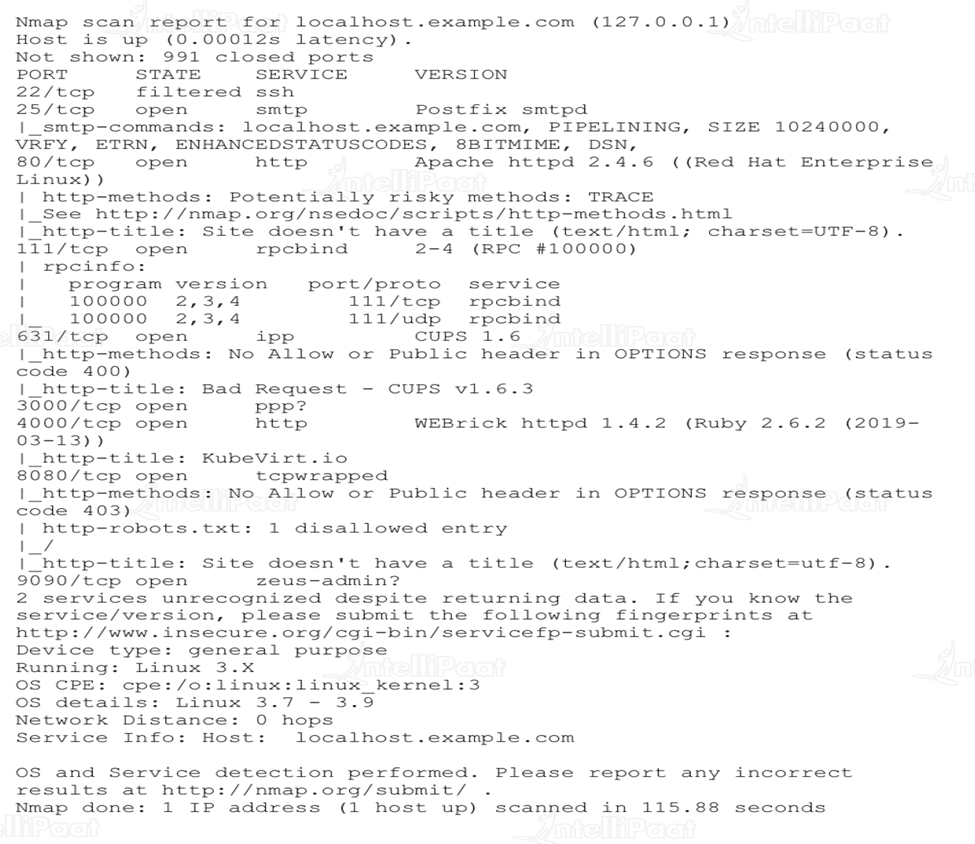
- Use Case Three
When conducting an inventory scan of your network, Nmap’s ability to determine a host’s operating system (OS) can be helpful. To learn the OS on a remote system, use the -A switch. For instance, jogging:
Nmap localhost.example.com -A
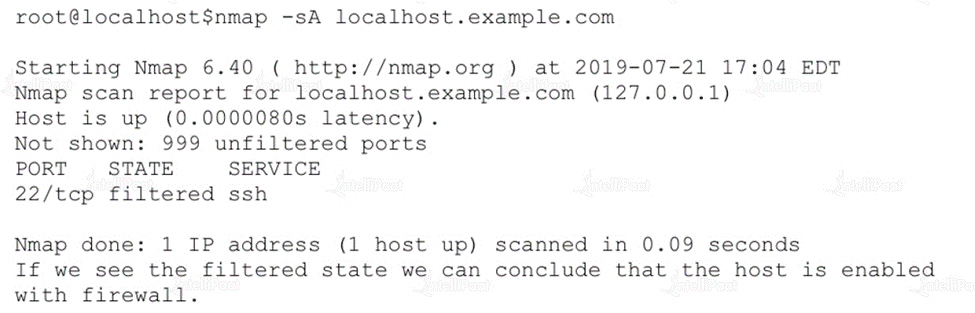
- Use Case Four
You can better comprehend the security issues affecting your network by using Nmap. Use -sA to see which ports are restricted and whether a remote host has a firewall configured. The word filtered in the report below indicates that a firewall is activated on this host:
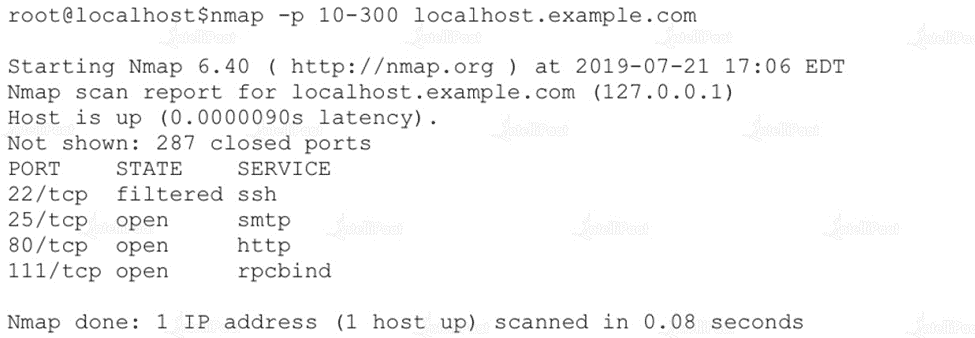
- Use Case Five
In order to determine which services are enabled on a host, we must first examine the open ports on that host (a practice that is well known). Nmap scans the range of ports given with the -p switch, as displayed below:
Courses you may like
Conclusion
Since Nmap provides a rapid, effective approach to auditing your systems, investing the time to understand it can significantly improve network security. Even the program’s most basic capabilities, like port scanning, enable you to instantly identify any suspicious devices that are operating on your network. I hope this blog helped you to gain information about the Nmap and its command used for penetration testing in the field of ethical hacking.
For more information on Ethical hacking, visit our Ethical Hacking Community
The post Nmap Commands – Complete Tutorial with Cheat Sheet appeared first on Intellipaat Blog.
Blog: Intellipaat - Blog
Leave a Comment
You must be logged in to post a comment.