What is Azure Virtual Network?
Azure Virtual Network (VNet) is the primary building block for your private network in Azure. VNet allows several types of Azure resources, including Azure Virtual Machines (VM), to securely connect with one another, the internet, and on-premises networks. VNet is similar to a traditional network in your own data center, but it includes extra Azure infrastructure features such as scale, availability, and isolation.
Table of Contents:
- Why use an Azure Virtual network?
- Advantages of using Azure Virtual Network
- Azure Vnet Capabilities
- Azure Virtual Network Architecture
- Azure Virtual Network limits
- Pricing
- Summary
Check out this Intellipaat Microsoft Azure Full Course video:
Why use an Azure Virtual network?
Azure virtual networks allow Azure resources to securely connect to the internet, and on-premises networks. A virtual network can be used to communicate Azure resources with the internet, communicate amongst Azure resources, communicate with on-premises resources, filter network traffic, route network traffic, and integrate with Azure services.
Advantages of using Azure Virtual Network
Several benefits of using the Azure virtual network are:
- It provides a safe environment for your applications.
- By default, a subnet in a VNet can connect to the public internet.
- We can easily route traffic from resources.
- It is a very secure network.
- It has excellent network connectivity.
- It simply creates complicated network topologies.
Want to read more about Azure? Go through this Azure Tutorial!
Azure Vnet Capabilities
Below mentioned are the capabilities of Azure Vnet:
- Isolation and segmentation: Virtual machines will be isolated from other resources when deployed into virtual networks. Because we’ve added the virtual machine to a virtual network, it can’t be accessed from the Internet or other Azure resources unless we permit connectivity between them. We can also employ subnets within virtual networks to further segment our network resources.
- Communication with the Internet: By default, all virtual network resources can communicate outbound to the Internet. However, it must create an inbound Internet connection. We have the option of using public IP addresses or load balancers.
- Communicate between resources: Communication between the virtual network’s resources or with other resources via service endpoints.
- Communication with on-premises resources: Your workloads in Azure virtual network can interact with workloads in our on-premises data center smoothly by deploying either a point-to-site VPN, a site-to-site VPN, or an Express route.
There are numerous features available within the Azure virtual network for traffic control:
- Filter network traffic: To filter traffic arriving at virtual network resources, we can utilize Network Security Groups, Application Security Groups, Azure firewalls, or third-party network virtual appliances.
- Route network traffic: We can route network traffic using routing tables, or we can set user-defined routes to route all outgoing traffic, for example, through a firewall.
- Monitor network traffic: You will be able to monitor both inbound and outgoing communications using network security groups and traffic analysis monitoring systems.
- Subnet: Subnet is important since various configurations will be performed at the subnet level. It is a set of IP addresses in the VNet. Vnet can be divided into numerous subnets based on various architectural concerns, such as deploying a virtual machine, App services environment, integration service environment, and so on. VMs and PaaS services are installed in separate subnets inside the same VNet and can connect with one another without any further configuration. Subnets are set up with route tables, NSG, service endpoints, and policies.
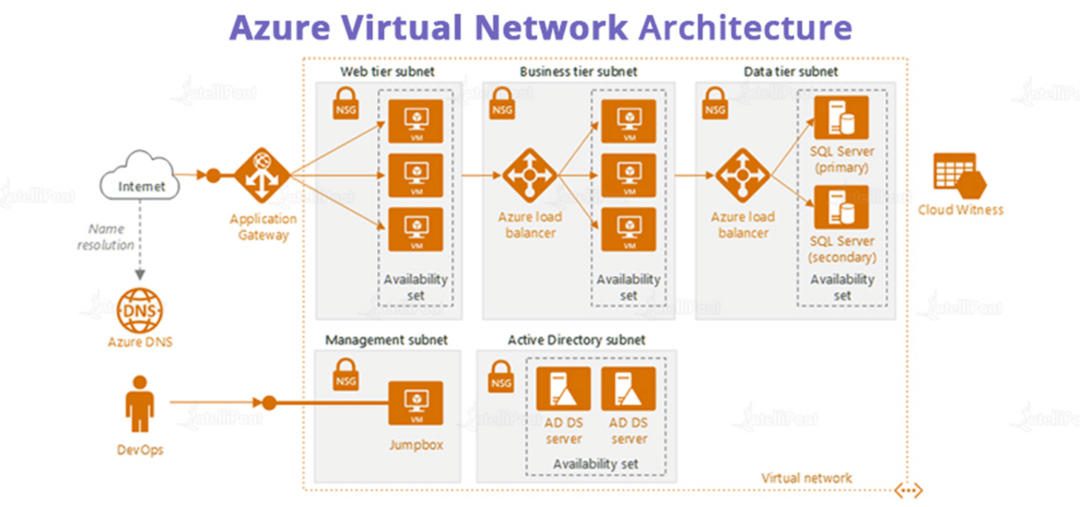
Azure Virtual Network Architecture
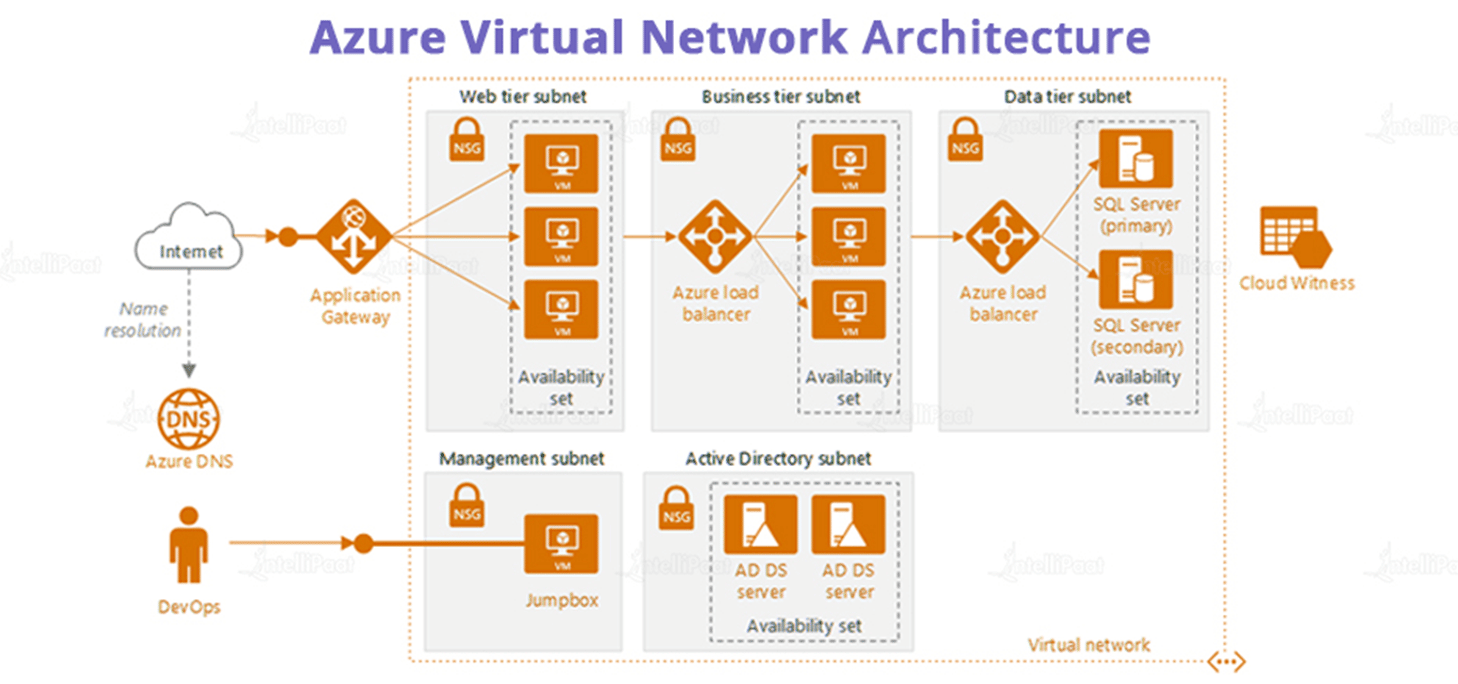
The diagram above depicts a common virtual network design for n-tier application architecture. The entire virtual network has been divided into subnets based on workloads such as the web tier, which contains the user interface, the business tier, which operates the business logic, and the data tier, which hosts the data source. The idea of creating and binding each group of Virtual machines into a different subnet is important in that we can assign one Network Security Group (NSG) to each subnet and manage the traffic flows across the tiers.
An HTTP request from the internet, for example, should not be sent immediately to the data tier subnet. We can assign an access policy to the Network Security Group of the Data Tier Subnet that only accepts inbound requests from the business tier subnet. Any additional requests made using a protocol other than the business tier and attempting to access the data tier will be rejected. Similarly, we can configure an access policy on the NSG of the business tier subnet so that the incoming request source IP address falls within the range of the web tier subnet. Furthermore, we can manage the traffic requests to Active Directory by placing them in a different Subnet within a Virtual Network.
If you have any doubts or queries related to Azure, do post them on Azure Community!
Career Transition
Azure Virtual Network limits
Only networking resources managed by Azure Resource Manager per region per subscription are subject to the following limitations.
| Resources | Limit |
| Virtual network | 1,000 |
| Subnets per virtual network | 3,000 |
| Virtual network peerings per virtual network | 500 |
| VPN gateways per virtual network | 1 |
| DNS servers per virtual network | 20 |
| Private IP addresses per virtual network | 65,536 |
| Private IP address per network interface | 256 |
| Private IP address per virtual machine | 256 |
Pricing
Azure provides a free Virtual Network. Each subscription allows for the creation of up to 50 Virtual Networks across all regions. VNET Peering connects two virtual networks, either in the same or different areas, and allows you to route traffic between them using private IP addresses (carry a nominal charge). At both ends of the peer networks, inbound and outgoing traffic is charged. Network equipment that run within a virtual network, such as VPN Gateway and Application Gateway, are also charged.
Virtual network peering:
Through virtual network peering, you can transport communication between virtual networks using private IP addresses. At both ends of the peer networks, ingress and egress traffic is charged.
VNET Peering within the same region
| Inbound data transfer | $0.01 per GB |
| Outbound data transfer | $0.01 per GB |
Courses you may like
Summary
A virtual network is a collection of IP addresses linked together. It is an important factor to consider while developing cloud-based applications. To secure each layer of application architecture within a highly secured network, it is recommended to build different subnets for different tiers of an application and attach each subnet to a network security group with limited inbound and outbound security rules.
In case you want to get certified and become an Azure Specialist, here is the course you are looking for Microsoft Azure Masters Program!
The post What is Azure Virtual Network? appeared first on Intellipaat Blog.
Blog: Intellipaat - Blog
Leave a Comment
You must be logged in to post a comment.