What is Azure Network Security Group(NSGs)?
Every second, billions of bits of data traverse the internet, transforming it into a global village for easy access and rapid transfer of information across multiple interconnected networks (both public and private networks).
As a result, monitoring, managing, and controlling various types of internet traffic is becoming increasingly difficult. Creating smooth communication between network devices has become a pipe dream with this rapid advancement. As a result, network devices are in higher demand, network architecture is becoming more complex, and maintaining smooth connectivity between networks and their respective endpoints is becoming more expensive.
The Topics Covered in this blog are:
- What is Azure
- What is Azure Network Security Group
- Azure Network Security Group-How it Works
- How to Create a Network Security Group in Azure
- Azure Network Security Group Rules
- Azure Network Security Group Best Practices
- Conclusion
Wanna Learn Azure, here’s an opportunity for you
What is Azure?
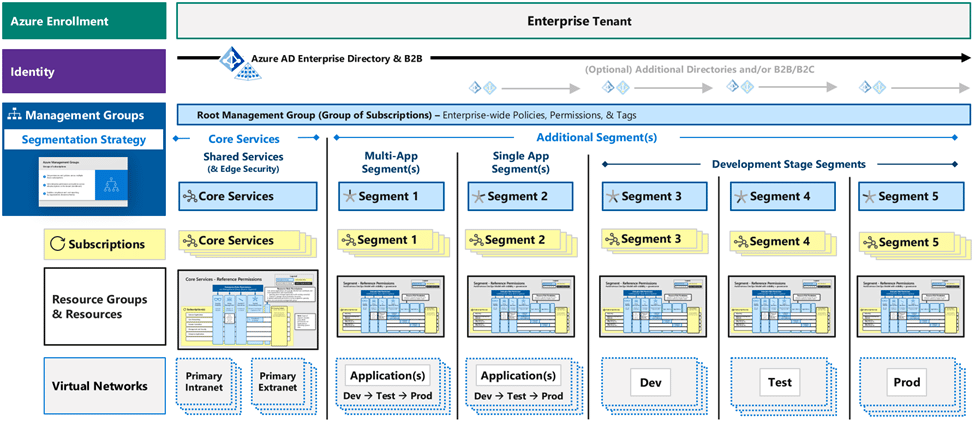
Azure is a cloud computing platform and an online portal that enables you to use and organize Microsoft’s cloud services and resources. These services and resources include collecting and converting your data based on your needs. All you need to access these resources and services is an active internet connection and the ability to connect to the Azure portal.
Did you know that Microsoft Azure and other public clouds are changing the way businesses deploy and secure distributed services? The reason for this is to instantly connect customers or apps from anywhere in the world to your service, providing them with a scalable and highly available virtual networking infrastructure. These networks are the first line of defense against attacks, and they should only accept traffic from specifically approved users, applications, or protocols. Keeping these networks secure can be difficult, but it is critical.
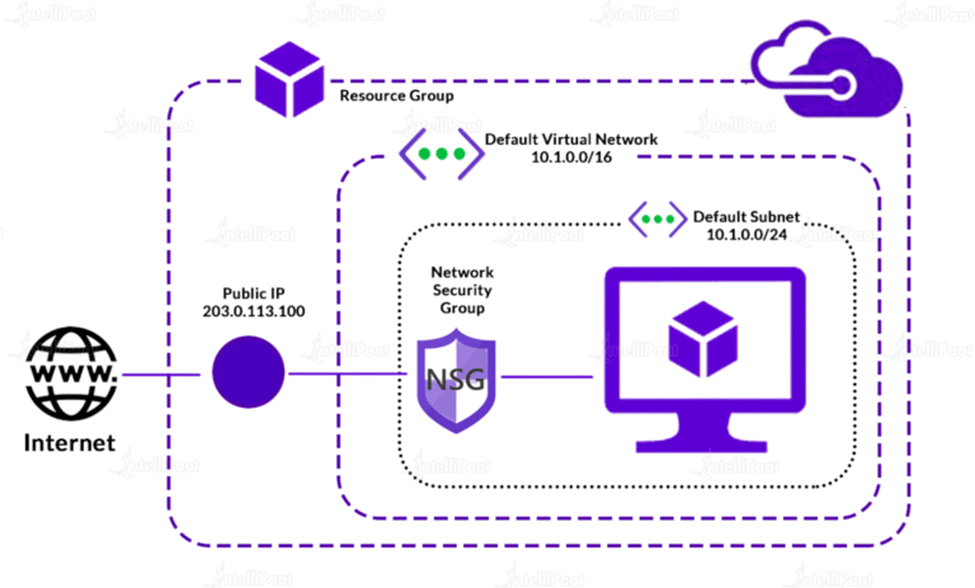
What is Azure Network Security Group
An Azure network security group is simply a collection of access control rules that can be applied to a virtual network or a subnet; these rules inspect inbound and outbound traffic to evaluate whether to approve or deny a package. The Azure network security is divided into two layers: the VM-level Network security group and the subnet-level Network security group.
Azure Network Security Groups from Microsoft is a fully managed service that helps refine traffic from and to Azure VNet. The Azure NSG is a collection of security rules that users can enable or disable as they see fit. These rules are evaluated using a five-tuple hash.
The 5-tuple hash uses the source port number, IP addresses, destination IP address and port number, and other variables. It works on OSI layers 3 and 4 and allows you to easily associate Network Security Groups with a VNet or VM network interface.
Excited about learning more about Azure? Enroll in our Microsoft Azure Training and get yourself certified.
Azure Network Security-How it works
Azure Network Security Group (NSG) from Microsoft is an excellent option for protecting virtual networks. With the help of this tool, administrators can easily arrange, filter, direct, and limit various network traffic flows. You can set different inbound and outbound rules to allow or restrict specific types of traffic when establishing Azure NSG. Individual rules should be created and configured if you intend to use Azure Network Security Groups.
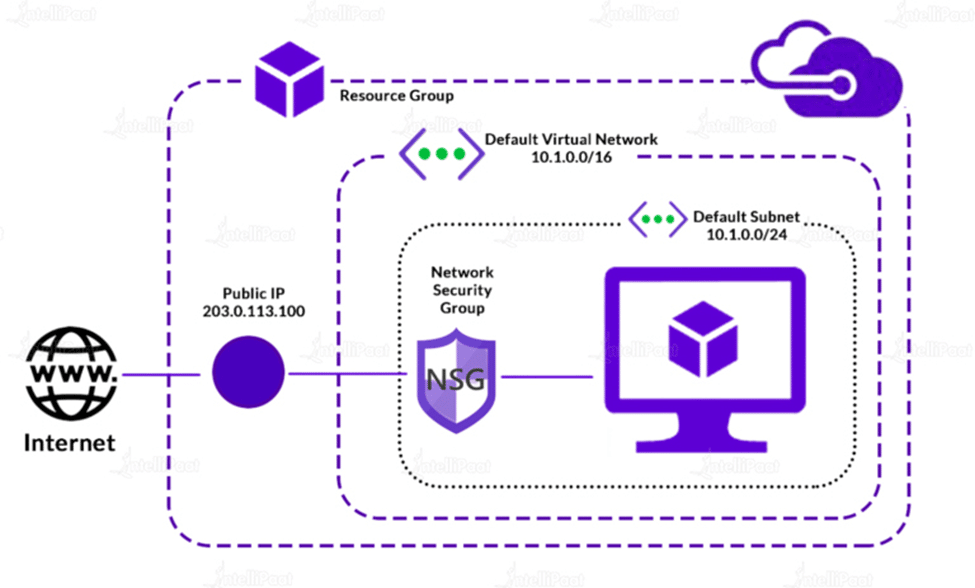
An Azure virtual network can contain resources from multiple Azure services. See Services that can be deployed into a virtual network for a complete list. Each virtual network subnet and network interface in a virtual machine can have zero or one network security group assigned to it. You can associate the same network security group with as many subnets and network interfaces as you want.
You can set any rules you want based on the situation, such as whether the traffic flowing through the network is safe and should be allowed.
Wanna Crack Azure Interviews like an Ace, here’s an opportunity for you Azure Interview Questions!
How to Create a Network Security Group in Azure
Follow this Process to Create a Network Security Group in Azure:
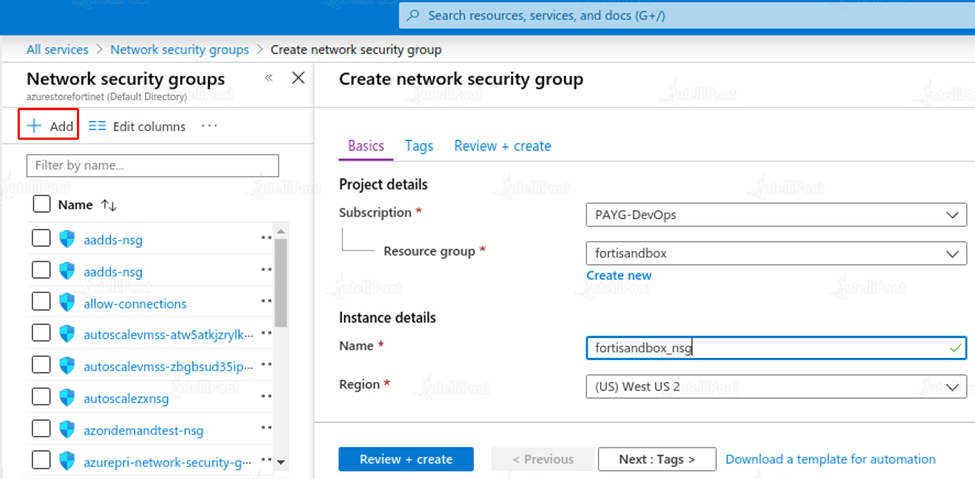
- On the Azure portal’s main menu.
- Alternatively, select Create a resource from the Home page.
- Now, choose Networking.
- Choose the Network security group from the list.
- Set values for the following settings in the create network security group page, under the basic tab
- Select Review + create.
- When you notice that the validation has passed the message, select the Create option.
There is a limit to the number of network security groups that can be created for each Azure location and subscription. For more information, see Azure subscription and service limits, quotas, and constraints.
Wanna Learn Cloud Computing from the Experts, here’s an opportunity for you Intellipaat Cloud Computing Course
Azure Network Security Group Rules
- Allow Vnet InBound – This rule allows all hosts within the virtual network (including subnets) to communicate without being blocked.
- Allow Azure LoadBalancer InBound – This rule permits an Azure load balancer to communicate with your virtual machine and send heartbeats.
- Deny All InBound – This is the deny-all rule, which by default blocks all inbound traffic to the VM and protects it from malicious access outside the Azure Vnet.
Learn more about Azure From our Azure Tutorial!
Azure Network Security Group Best Practices

- NSG Flow Logging: Flow logging is a feature of Azure network watcher for NSGs (Network interface logging level). Flow logs are sent to the storage account you specified during setup once enabled. The flow log information is displayed in JSON format. The output includes both incoming and outgoing traffic, with flows displayed on a per basis rule basis.
- NSG Rule Priority: NSG rule priority is one of the best practices for Azure network security groups. NSG rules are implemented in a priority order ranging from 100 to 4,096, with each new rule being added incrementally.
Rules are inspected at the micro level. Each rule is examined in priority order. Once one rule matches the traffic, the remaining rules are not examined any further.
If traffic matches rule 110, for example, it will be transmitted by this rule. It is something to consider if multiple rules are attempting to overlap.
Career Transition
- Naming convention: Although it may appear silly, a proper naming convention from the start can make the support process much easier! Best practices for Azure NSGs include naming each rule appropriately, such as:
As an example: ‘WebServerProduction-to-DatabaseProduction-SQLConnection,’ unlike ‘Rule35-SQL,’ is not the same thing
- Consider your options before deploying (Group Rules & Ports): Do you understand the scope of the rule? Do you know what rule set you’re going to start with? Best practices for Azure network security groups include using IP ranges instead of a series of sequential IPs, along with ports in the following format:
192.168.1.0/24 as opposed to 192.168.1.1, 192.168.1.2, and so on?
Why not 80-82 instead of 80,81,82?
Both of these suggestions would reduce the overall number of NSG regulations.
- One National Security Group to rule them all: Is having an NSG for each subnet necessary? Or even by VNET? In most cases, you can aggregate one NSG across multiple NICs, Subnets, or even VNets.
The default number of rules in an NSG is 200, and the maximum number of rules in an NSG with a support ticket is 1000. Unless you reach this limit, multiples are not required!
Courses you may like
Conclusion:
Azure network security groups are well-known for their ability to assist you in managing network security more quickly and efficiently. While configuration may appear to be time-consuming at first, service tags and application security groups can help.
To aid in the security and defense of your Microsoft cloud infrastructure, make NSG planning and management a part of your regular Azure operating procedures moving forward.
You are doubts get resolved on Intellipaat Azure Community Page
The post What is Azure Network Security Group(NSGs)? appeared first on Intellipaat Blog.
Blog: Intellipaat - Blog
Leave a Comment
You must be logged in to post a comment.