What is a Computer Virus?
As long as computers have been stable enough, people have managed to find ways to cause problems, and one of the most effective ways to create mischief on a computer is through malware such as a computer worm or virus.
Let us look at the topics covered in this blog:
- What is a Computer Virus?
- History of Computer Virus
- How do Computer Viruses Spread?
- Types of Computer Virus
- Top 10 Computer Virus
- Effects of Computer Virus
- How to Prevent Computer Virus
- How to Remove Virus from Computer
- Conclusion
Before going any further, look at this video in which our cybersecurity specialists explain the various cyber threats.
What is a Computer Virus?
We hear about it in the news almost weekly these days but what is a computer virus?
A virus is also software, a piece of code that has the ability to self-replicate. A virus can spread quickly from one computer to another and result in abnormal performance. A virus is a sort of malware; it attaches itself to the host file to get executed and spread all over the system.
A virus replicates itself by creating files and attaching itself to genuine software, allowing the user to run the virus. A virus can only spread with human interaction.
A computer virus is a program that disrupts the normal working of a computer without the user’s knowledge. A computer virus attaches itself to the files stored on the computer and damages them. When the replication succeeds, the affected areas are said to be infected with a computer virus.
A computer virus is a malicious piece of software or malware that, once it gets inside your computer, replicates and infects other computers in your network, stealing passwords, data, logging keystrokes, corrupting files, spamming your contacts, or even taking over your machine.
History of Computer Virus
Viruses were created for nefarious objectives. People generate viruses for a variety of purposes, ranging from harmless fun to malicious destruction.
The concept of an autonomously self-replicating entity dates back to the 1940s. Creeper was constructed and deployed onto the ARPANET in 1971; Creeper would bounce between computers, leaving only a message written on the teletype terminal, “I’m the creeper, catch me if you can.” Later versions of the program would drop a duplicate of itself on the visiting machine, making Creeper the first application to spread copies of itself autonomously on other systems. Thus, Creeper was the first computer virus created.
Another virus known as Elk Cloner would add itself to the system’s boot sector and be used to boot Apple devices, which would then add the cloner to every subsequent disc placed into the system by writing into the boot sector.
Have a look at Intellipaat’s Cyber Security courses and sign up today!
How do Computer Viruses Spread?
There are six common ways through which viruses spread.
- Opening attachments or links from unknown and fake emails: This is one of the most popular methods to infect with a virus or ransomware. Emails are spoofed to appear authentic; they contain an attachment or link that will infect your machine when clicked. These counterfeit emails are so well-crafted that even a seasoned professional can be caught off guard, if not careful.
- Downloading software from malicious sites: When your computer gets infected with a virus, it is common for you to think that it might not be a trusted website. It is a common misconception that viruses only come from inappropriate or problematic websites. But viruses are dangerous and are everywhere on the internet.
- Online ads: Malicious internet adverts, often known as malvertising, are yet another way for your computer to be infected with a virus without your knowledge or traceability. Criminals frequently install clean advertising on trusted websites and leave them there for some time to establish credibility. After some time has passed, they insert a harmful code inside the ad that, when clicked on, infects your computer.
- Social media: People are generally more relaxed about clicking on links published on social media sites. Malicious links on social media sites may contain viruses that may be harmful to your computer or any other device.
- Unpatched software: Another way you put your computer at risk of a virus infection is through unpatched software. Security holes, unknown to the software makers or anti-virus vendors, are also known as zero-day vulnerabilities.
- Pirated software: An illegal copy of software is called pirated software. Some companies intentionally add a virus to pirated software.
Types of Computer Viruses
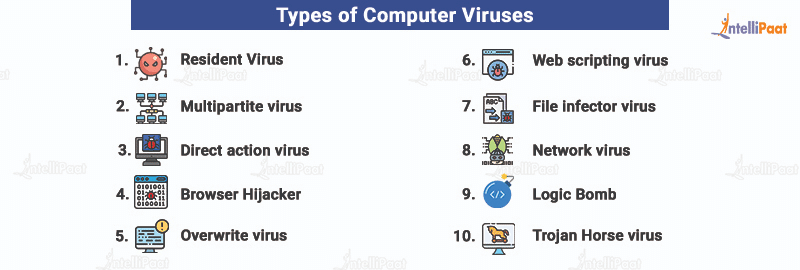
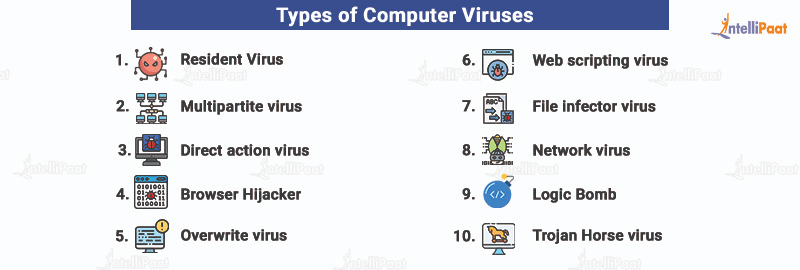
The different types of computer viruses are:
- Resident virus: Resident virus sets up shop in your RAM and meddles with your system operations. It is so cunning that it can attach itself to anti-virus software files.
- Multipartite virus: This virus infects the entire system. This virus is spread by performing unauthorized actions on your operating system, folders, and programs.
- Direct action virus: This virus targets a specific file type, most commonly executable files (.exe), by replicating and infecting files. Due to its targeted nature, this virus type is one of the easier ones to detect and remove.
- Browser hijacker: This type of virus is easily detected. It infects your browser and redirects you to malicious websites.
- Overwrite virus: As the name implies, overwrite virus overwrites file content to infect entire folders, files, and programs.
- Web scripting virus: This sneaky computer virus disguises itself in coding links, ads, images, videos, and site code. It can infect systems when users download malicious files or visit malicious websites.
- File infector virus: By targeting executable files (.exe), the file infector virus slows down programs and damages system files when a user runs them.
- Network virus: Network virus travels through network connections and replicates itself through shared resources.
- Logic bomb: The logic bomb virus is triggered by a specific condition, after a certain number of transactions, or on a specific date and time. This virus is also called a time bomb.
- Trojan Horse virus: This virus performs illegal and damaging instructions in the middle of a program such as a computer game. This virus includes concealed instructions to wipe data such as formatting the C drive, which could result in massive data loss.
Preparing for an Ethical Hacking job interview? Have a look at our blog on Ethical Hacking interview questions and start preparing!
Top 10 Computer Virus
Examples of computer viruses are given below:
- Conficker: Conficker was released into the wilds of Windows to steal administrator passwords and create a botnet. It infected 15 million corporate, government, and home PCs, making it the single largest computer virus infection in the last five years, causing nine billion dollars in economic damage.
- SQL Slammer: SQL Slammer spreads so rapidly that 75,000 infections occurred within a span of 10 minutes. It is a denial-of-service attack that targets users’ favorite websites causing them to crash.
- Stuxnet: Computer viruses are usually more of a nuisance or costly problem than a highly-engineered weapon capable of causing real-world damage. Stuxnet may have been the first weapon entirely made out of code. It was used for the specific purpose of taking down rands. Stuxnet is considered the most dangerous computer virus.
- Boot sector virus: Boot sector is the first sector of the hard disk where the boot program is stored. The boot program loads the operating system to the memory. The virus attaches itself to executable files, .exe, .com, and .dll; when users use these files, the virus is activated. It affects the booting process of an infected computer system.
- Chernobyl virus: Chernobyl virus deletes all Microsoft Office files and destroys all computer data when an infected file is executed. Chernobyl virus also deletes the partition information from the hard disk, causing a major loss of data.
- Redlof: Redlof is a polymorphic virus built in a visual basic script. This virus embeds itself, without any attachment, to every email sent from the infected system. It attacks a file named folder.sst.
- Macro virus: Macro virus is a computer virus that is inserted as a macro in a document. A macro is a sequence of commands that could be stored and recalled with a single command.
- Code Red: Code Red wreaked havoc and annoyed users all over the internet. Code Red also launched a denial-of-service attack and targeted the White House’s website.
- Storm virus: Storm virus was a backdoor Trojan Horse that was released on the internet back in January 2007 to infect computers running Microsoft Windows’s operating systems.
- Sasser and Netsky: Sasser is connected to the Netsky family of viruses that attack vulnerable PCs through an open port, which is what your firewall protects against. The release of Sasser in 2004 caused widespread problems.
Courses you may like
Effects of Computer Virus
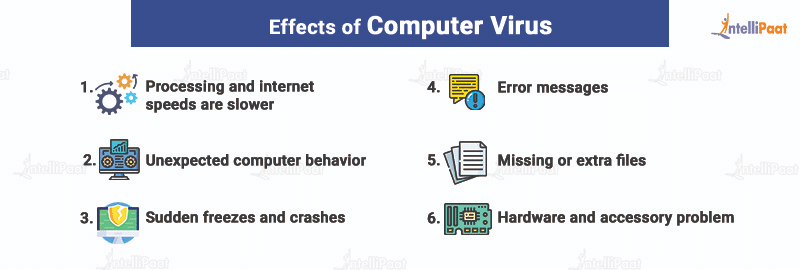
The following are the effects of a computer virus:
- Processing and internet speeds are slower: A slower computer does not always indicate the presence of a virus, but if there is a significant shift in speed, then there is a chance that your computer is affected by a virus and it is better to check the system for the same.
- Unexpected computer behavior: A virus can do all kinds of strange things to your computer. If your computer stops responding to clicks, decides to open files on its own, scrolls, or acts as if a key has been pressed when it has not, then the system is probably affected by a virus.
- Sudden freezes and crashes: Because viruses damage the hard drive, they can cause your computer to experience a catastrophic failure.
- Error messages: Your computer knows that something is wrong before you do. One of the most noticeable effects of a computer virus is the sudden appearance of pop-up messages warning you about missing system or application files.
- Missing or extra files: Keep track of the size of your hard drive. A virus can install files of itself or unwanted files on your computer. Viruses can also delete files unexpectedly.
- Hardware and accessory problem: If you suddenly have a problem with your computer’s display, such as mixing pixels or color problems, it can be a sign of a virus messing with your system.
How to Prevent Computer Viruses
We rely on computers for a variety of tasks. We place our trust in them to keep our information safe, including our files and personal data, which is why it is critical to protect your computer and do everything you can to keep it functioning.
Here are some tips to protect to prevent viruses:
- Anti-virus software, such as Kaspersky, Norton, or Windows Defender, should be used. Anti-virus software prevents viruses from being installed and also allows you to search your computer for viruses and remove them if any are discovered. Remember that no anti-virus program is perfect; so, to keep secure, avoid suspicious-looking adverts or downloads and frequently run anti-virus program updates.
- Do not click on any pop-up adverts.
- Make sure that your operating system is up to date as well.
- When accessing unsolicited emails, inspect them thoroughly.
- Carefully analyze the documents acquired from file-sharing websites.
Enroll in the Ethical Hacking course offered by Intellipaat and train under their experts.
How to Remove Virus From Computer
If your PC is infected with a virus, you can get rid of it by following the below-mentioned instructions:
- Start in Compatibility Mode. The procedure will differ depending on the Windows version or any other operating system you are using.
- Remove any registry entries. Use the repair disk program to erase the temp. folder while in standby mode.
- Get legitimate and on-demand antivirus software.
- Start the on-demand scanner first, then the legitimate scanner. If neither scanner eliminates the virus, it may be necessary to remove the virus explicitly. This can only be done by a professional who is familiar with the Windows Registry and knows how to inspect and delete system and program files.
- Reinstall any files or programs that have been corrupted by the malware.
Career Transition
Conclusion
I hope this blog gives you some insights on computer viruses and how to protect yourself from them. In this era of digitalization, cyberattacks are becoming more common with every passing day. So, it is our responsibility to be safe from malicious viruses and other sources of attacks.
Having doubts? Shoot them right away to our Cyber Security community!
The post What is a Computer Virus? appeared first on Intellipaat Blog.
Blog: Intellipaat - Blog
Leave a Comment
You must be logged in to post a comment.