Strategy-Building Using Free-Form Search Knowledgebases
Blog: KWKeirstead's Blog
I have been following the work of the Architecture Thinking Association for about one year and have been impressed with the work of this organization.
In a recent LinkedIn post, the founder, Wolfgang Goebl, states that “Most IT landscapes of larger companies consist of hundreds of applications that are interconnected via poorly designed interfaces.”
Note the two issues raised i.e., “interconnected applications” and “poorly designed interfaces”.
The mess IT is in comes in the main from picking solutions instead of analyzing requirements and the pre-cursor to analysis is to put in place a process for building a list of requirements.
Our group has used the following model for enterprise-wide strategy building over 30 years.
InfrastructureResources -> Capabilities -> Prospective Initiatives (problems or opportunities) -> RisksVulnerabilities -> Ranking of Initiatives -> Shortlisting (ROI/SROI, business fit) -> Funding a few Initiatives
We knew from RBV (Resource-Based View) that organizations make better decisions when staff are able to “view/see” the factors impacting decisions and build platforms that made it easy for strategists to consolidate data for conversion to information and knowledge. To this end, we implemented methods and tools at platforms that made it easy to onboard business analysts.
Here below are two screen images illustrating how not to build strategies and how to build strategies.
Image 1
What we have below is a shadow ontology of some 1,000 nodes belonging to eight (8) Entities (Suppliers, Business Partners, Competitors, Country Profiles, Customers, Standards, Best Practices, Reference Material).
The application is for Improvised Explosive Device (IED) detection Command and Control.
Each Entity is a shallow hierarchy with NO crosslinks between any node in one Entity that may have something in common with other nodes in other Entities and such other nodes.
The time to construct this shadow e-map was a small fraction of the time that would have been needed to put in place “all” of the possible links across the multi-root hierarchy that has the focus.
Full mapping for this “business development” application would have taken several months resulting in over 100,000 linkages, with no guarantee that the analysts would succeed in putting place all possible linkages.
The secret-sauce is to let the search engine build linkages “on-the-fly – user of the platform can launch searches and save the configuration of ‘hits’ or not save.
Bottom line:
Easy to build (the construction can be automated from ordinary delimited text “records”), fast to build, but not a very friendly user interface.
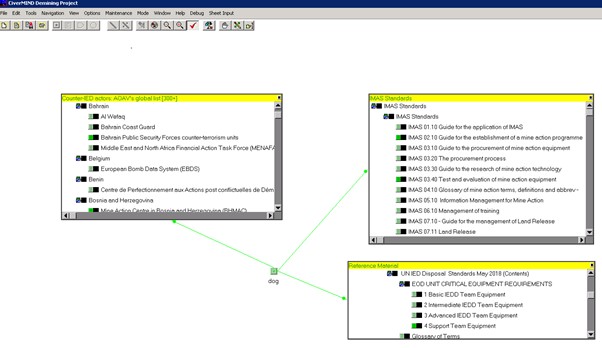
Image 2
Here is the same content, with nodes organized under eight “outline” Entities.
Processing by blur.imageonline.co
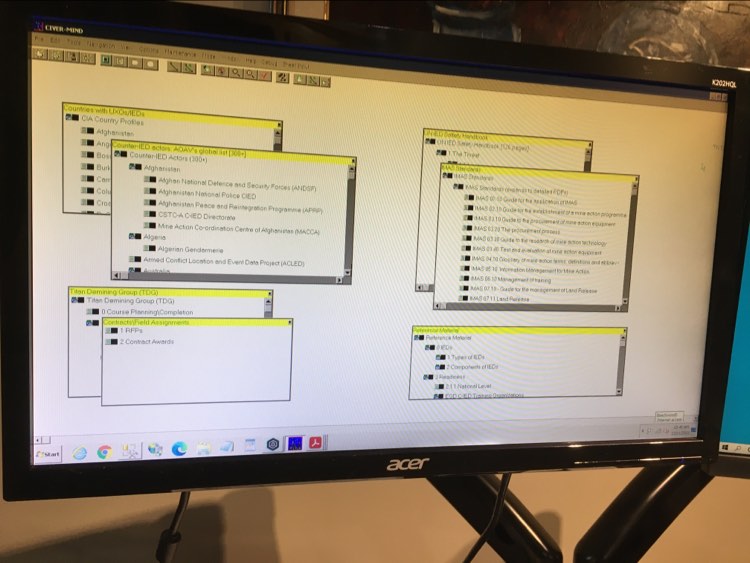
A search for ‘dogs’ yields 22 hits.
Note that the number of visible Entities has been reduced to three (3), with highlighting of the ‘hits’ in green.
Bottom line:
Launch a search, the search engine highlights the ‘hits’ and masks any Entities where there are no ‘hits’.
Clicking on any node results in pop-up of the underlying document, text, or images.
Examples: (Improvised Explosive Device Detection Command and Control)
- show actors that use sniffer dogs, by IED actor, by country, reduce clutter at Entities where there are no ‘hits’.
- Build, via drag and drop, outlines comprising cloned of certification standards, per field operator, for tracking of progress.
- Set up Entities for various IED work sites, allocate moveable resources to the, track their use, ensure return to sourcing warehouses.
Leave a Comment
You must be logged in to post a comment.








