Recap — Process Mining at BPM 2012
![]()
This year’s BPM conference was loaded with contributions in the process mining area. We started off with our BPI keynote talk Tales from a Process Mining startup, where we spoke about both the challenges we faced when starting Fluxicon as well as some of the opportunities that practical problems present to the process mining research community.
In the Q&A; after the talk someone asked what process mining researchers can do to better reach practitioners with their work. One commenter suggested that the first and most easy thing to do is to make sure you put all your publications online1, because people outside of universities2 do not have subscriptions to Springer, IEEE, or ACM.
When putting together the links to the process mining papers from this year’s conference for this blog post, I noticed that the problem has slightly improved: I had to hunt down only about 25% of the publications while the remaining papers were already available on the authors’ websites. From the 25% of the authors that I contacted I either obtained a link or permission to make the pre-prints available.
So, let’s dive into our recap tour to see what is new at the process mining front!
BPI Workshop
On the first day, the Business Processing Intelligence (BPI) workshop, one of the primary targets for process mining researchers over the past eight years, presented five full papers and three short papers on process mining-related topics.
Full papers:
Alignment Based Precision Checking by A. Adriansyah, J. Munoz-Gama, J. Carmona, B.F. van Dongen and W.M.P. van der Aalst presents a meta evaluation approach for precision metrics (a quality measurement that ensures that a discovered process model is not too generic but reflects the observed reality closely).
A Hierarchical Markov Model to Understand the Behaviour of Agents in Business Processes by D.R. Ferreira, F. Szimanski and C.G. Ralha addresses the problem that event logs are often available on a more fine-grained level than the high-level business process steps one has in mind (and suggests an approach to create a two-step mapping from the event log to a detailed model and from the detailed model to the higher-level activities).
End-to-End Process Extraction in Process Unaware Systems by S. Goel, J. Bhat and B. Weber identifies a number of challenges and presents an approach for when log data for process mining need to be extracted from a system landscape across multiple applications (illustrated with a purchase order process case study).
Root Cause Analysis with Enriched Process Logs by S. Suriadi, Chun Ouyang, W.M.P. van der Aalst and A.H.M. ter Hofstede discusses an approach to extend existing log data by additional context information to allow for data mining-supported root cause analysis (using the example of the workload of employees).
Process Mining and the ProM Framework: An Exploratory Survey by J. Claes and G. Poels presents the results of an online survey of 90 people who answered questions about, for example, the benefits of process mining, which ProM plug-ins they use, and which process mining tools they have heard of.
Short papers:
MANA: Identifying and Mining Unstructured Business Processes by P.M. Esposito, M.A.A. Vaz, S.A. Rodrigues and J.M. Souza presents a tool, where an instance database can queried and filtered, for example, based on placeholders in a freetext field (disposing%comp% matches ‘disposal of computer equipment’ and ‘disposal of computer material’) to select process instances for process mining.
An Experimental Evaluation of Passage-Based Process Discovery by H.M.W. Verbeek and W.M.P. van der Aalst shows how it helps to split up the event classes over multiple event logs by using so-called passages – a way to decompose process mining problems – to reduce the complexity (run time) of process mining algorithms.
Predicting Deadline Transgressions Using Event Logs by A. Pika, W.M.P. van der Aalst, C. Fidge, A.H.M. ter Hofstede and M. Wynn presents a method for the automatic discovery of likely deadline overruns based on time-related process patterns in the event log (tested using the BPI challenge log).
Other Workshops
In the break people had the chance to switch to other workshop sessions. Process mining papers were also presented in other workshops that were held in parallel to the BPI workshop. Here they are.
DAB Workshop
In the new Workshop on Data- and Artifact-centric BPM (DAB) two paper were related to process mining:
From Petri Nets to Guard-Stage-Milestone Models by V. Popova and M. Dumas defines a translation method from Petri nets, in which most process discovery techniques produce their models, to GSM models (which represent business processes around business-relevant milestones), to make GSM models available for process mining end users.
Automatic Discovery of Data-Centric and Artifact-Centric Processes by E. Nooijen, B. van Dongen and D. Fahland combines techniques for schema discovery, schema summarization, log extraction, and life-cycle discovery to extract data from ERP systems for process mining of data-centric processes (e.g., a process evolving around the ‘quote’ and ‘order’ business objects).
ProHealth Workshop
The ProHealth workshop had the following two process mining papers:
Embedding Conformance Checking in a Process Intelligence System in Hospital Environments by N. Herzberg, A. Rogge-Solti, M. Weske and K. Kirchner introduces a method to conformance checking that computes fitness of individual activities in the setting of sparse process execution information in hospitals (in situations, where not all activities of a patients treatment are logged).
Process Mining in Healthcare: What Data is Available and Which Questions can be Solved? by R. Mans, W.M.P. van der Aalst, R. Vanwersch and A. Moleman describes the different types of event data found in current Hospital Information Systems (HISs) and discusses open problems and challenges that need to be solved in order to increase the uptake of process mining in healthcare.
SBP Workshop
At the Joint Workshop on Security in Business Processes (SBP) two papers were presented:
A Case Study on the Suitability of Process Mining to Produce Current-State RBAC Models by M. Leitner, A. Baumgrass, S. Schefer-Wenzl, S. Rinderle-Ma and M. Strembeck investigates the applicability of four process mining techniques (role derivation, role hierarchy mining, organizational mining, and staff assignment mining) to discover access control information from event log data.
A Process Deviation Analysis Framework by B. Depaire, J. Swinnen, M. Jans and K. Vanhoof presents a framework that structures the field of process deviation analysis and identifies new research opportunities, starting from a set of managerial questions.
TAProViz Workshop
Finally, the Workshop on Theory and Applications of Process Visualization (TAProViz) had one paper on process mining:
Visualizing the Process of Process Modeling with PPMCharts by J. Claes, I. Vanderfeesten, J. Pinggera, H. Reijers, B. Weber and G. Poels studies the process of process modeling to understand, for example, in which order a process modeler adds start and end events, activities, gateways, edges, etc. (using an adapted dotted chart implementation).
BPI Challenge
At the end of the BPI Workshop, the winner of the BPI Challenge was announced. The BPI Challenge is an annual process mining challenge, where a real dataset is anonymized and put up for anyone to analyze. Submissions are then judged by a jury and a winner is selected.
This year’s data set was the event log of a loan application process at an undisclosed Dutch financial institute. You can read an interview with Boudewijn van Dongen, the organizer of the challenge, about the background and motivation of the BPI challenge on our blog.
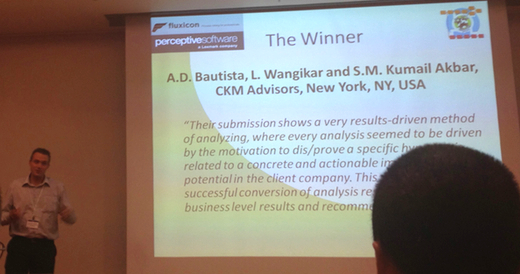
This year’s challenge had a couple of really good submissions and it was difficult to choose a winner. In the end the jury decided to give the award to A.D. Bautista, L. Wangikar and S.M. Kumail Akbar from CKM Advisors, New York, USA.
According to the jury:
Their submission shows a very results-driven method of analyzing, where every analysis seemed to be driven by the motivation to dis/prove a specific hypothesis, related to a concrete and actionable improvement potential in the client company. This results in a successful conversion of analysis results in digestible business level results and recommendations.
I recommend to read the winning analysis report of the CKM Advisors group to see how the authors succeeded in extracting actionable insight and understanding of the situation behind the process. You can also watch our video interview with Lalit Wangikar, one of the authors, to hear more about their approach.
Make sure you also take a look at the other submissions, because they all excel in different areas and it’s very interesting to see how they tackle the same event log with different approaches.
Here are the remaining submissions to this year’s BPI challenge, in alphabetical order:
A. Adriansyah and J.C.A.M. Buijs from Eindhoven University of Technology, The Netherlands follow an iterative approach based on process discovery and alignment techniques to increase the quality of the models. They mine process models fist per subprocess and then as a whole. Once the models have sufficient quality, they are replayed for performance analysis purposes.
R.P. Jagadeesh Chandra Bose and W.M.P. van der Aalst from Eindhoven University of Technology, The Netherlands were the runner-up as they succeeded in extracting the most detailed information out of the process data. Using hierarchical classification to simplify the log, they report results from a resource, control-flow, and diagnostics perspective. They even developed a dedicated Resource Work Analysis ProM plug-in for this challenge.
C.J. Kang, C.K. Shin, E.S. Lee, J. H. Kim and M.A. An from Myongji University, South Korea describe an explorative analysis process and take great care to reveal the thinking behind their approach, including the limitations they encountered. Their broad exploration of various process questions leads them to dive deeper into several areas for further investigation.
T. Molka, W. Gilani and X.J. Zeng from SAP Research, Ireland illustrated how powerful the dotted chart analysis tool can be for process analysis. They extracted a variety of patterns, such as the distribution of work across the work day, when activities are cancelled, or when new resources join the workforce.
H.M.W. Verbeek from Eindhoven University of Technology, The Netherlands focuses on the Transition System Miner and shows how the miner can used to obtain insights into the control-flow, data perspective, and resource perspective. He also illustrates that the company does not use case managers, because many handovers occur between employees on the same application.
If you are curious to follow some of the results in Disco, import this project file with the challenge log in the demo version of Disco and see for yourself!
Meeting of the IEEE Taskforce for Process Mining
After the BPI workshop, the IEEE Taskforce on Process Mining held their annual meeting. The minutes and slides of the meeting are available online.
The main points that were discussed are:
- The XES Standard, which has already been accepted by the IEEE Task Force as the commonly agreed-upon format for event log data interchange, is now on a path to becoming an accredited IEEE Standard. To drive this process, a working group has been formed that creates the proposal and puts it up for comments. The final proposal is planned for submission in April 2013.
The working group consists of: Wil van der Aalst, Christian Gnther, Eric Verbeek, Keith Swenson, Moe Wynn, Lijie Wenn, and Michael zur Muehlen.
-
It has been proposed to restructure the Task Force by listing organizations rather than individuals. The reason for this proposal is that the task force has grown a lot and it is hard to keep an overview and address everyone in this long list. The new structure would be such that there is one contact person per organization and possibly several additional active members.
-
Promoting and informing about the topic of process mining is one of the main goals of the task force, and there are many initiatives that are ongoing. Members were encouraged to inform the list about activities that are relevant to the objectives of the task force (past and future events and initiatives are also listed in the annual task force meeting minutes). Furthermore, it was discussed how even more activities can be stimulated in general and from inactive members.
Demos
The Demos were held on Tuesday, the first conference day, at the end of the afternoon. Ten tools were presented in five rooms in three consecutive sessions (people could switch and see six out of the ten demos).
We already told you earlier that we are proud that Disco, our professional Process Mining software, has won the Best Tool Demonstration award at the BPM 2012 conference!
In our room was also the process mining demo of Eventifier, which appears to be a nice tool for correlating and extracting logs from a database. With its XES export it is compatible with both Disco and ProM 6.
Keynote of Wil van der Aalst
Although Wil van der Aalst’s keynote on the morning of the second conference day was not specifically about process mining, process mining did play a role. He looks at ten years of BPM conferences and dissects the discussed topics into 20 use cases. The process mining spectrum is covered by several of these 20 use cases.
You can check out the slides or watch the video recording of Wil’s talk.
BPM Process mining session
At the second conference day, there was a process mining session at the main conference, and because the conference organizers videotaped the main conference talks you can actually watch all these presentations online.
Sandy Kemsley also covered the process mining talks in her well-known explanatory summary style. You can read these more detailed summaries on her blog.
Here is a quick overview:
Repairing Process Models to Reflect Reality by D. Fahland and W.M.P. van der Aalst addresses the problem that while differences between the observed behavior and a process model can be detected and diagnosed, the actual repair of the model (assuming that the model should be adjusted) is not supported. They propose a technique for repairing a process model with respect to a log in such a way that the resulting model is as similar as possible to the original model.
Where Did I Misbehave? Diagnostic Information in Compliance Checking by E. Ramezani, D. Fahland and W.M.P. van der Aalst presents a new compliance checking approach based on Petri net patterns and alignments. To check compliance with respect to a rule, the event log describing the observed behavior is aligned with the corresponding pattern, which allows for both a quantification of compliance and intuitive diagnostics explaining deviations at the level of alignments.
FNet: An Index for Advanced Business Process Querying by Z. Yan, R. Dijkman and P. Grefen proposes a new technique to query large collections (hundreds or thousands) of process models. The focus here is on the efficiency of retrieval of models that satisfy the query, and based on experiments it is shown that the technique performs on average two orders of magnitude faster than existing techniques.
Using MapReduce to scale events correlation discovery for business processes mining by H. Reguieg, F. Toumani, H.R. Motahari Nezhad and B. Benatallah looks at distributed event correlation to support log creation for big data sets. They propose a two-stages approach to compute correlation conditions and their entailed process instances from event logs using the MapReduce framework and evaluate the scalability of their algorithm.
Practitioners’ day
At the last day, we had the chance to talk about process mining in the BPM Practice session. This session was mostly visited by Estonian practitioners, not so many researchers. We got great reactions and many people told us that they recognized the problems of subjectivity and lack of evidence in their process improvement projects today.
That’s it! We hope we could give you an overview and some pointers to dig deeper into the state-of-the art of process mining research.
Please let us know whether you found this useful and drop us a note if we missed something.
Leave a Comment
You must be logged in to post a comment.