Password and Human Factors
Blog: Collaborative Planning & Social Business
My company has be going once again through data security training. That is not in itself bad, but the misguided and outdated instructions are making me ill. Why can the “security” experts learn?
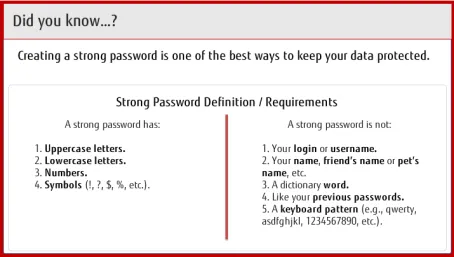
We are presented with this guidance:
We SAY we are human-centric, but we are not.
The most important aspect of a strong password, is that it is easy to remember. A hard to remember password will be written down … because it is hard to remember. Duh!
Writing down passwords is a security flaw. Duh again!
Therefor, it is quite clear that for a strong password to be successfully used, it must be at the same time easy to remember. It is not hard to make a strong password that is easy to remember. You can make a password that is easy to remember without violating any of the rules on the right side.
The strongest password you can create is a list of letters that correspond to a complete phrase that you are familiar with. Take a phrase that you know, but is obscure, probably something personal to you which you can easily remember, but nobody would necessarily know it is associated with you. For this example I am using a very popular phrase, but you should not use a popular phrase.
“Now is the time for all good men to come to the aid of their country”
You password is the first letters of all the words: “nittfagmtcttaotc”
That is a strong password. Try it. If you know the phrase, it is easy to type. It is virtually impossible for a password generator to guess this.
Adding uppercase, punctuation, and number (“Nittfagmtcttaotc5!”) makes this a little harder to guess, but not really very much. I know, everybody is going to require mixed case punctuation and numbers so you have to have it, but it does not make the password much stronger. These things only make a very weak password stronger.
You can have the strongest password in the world, but if you have to write it down, then all advantages of a strong password are lost.
Why do these “security people” always forget that human factors is the single largest cause of unauthorized access?
It continues with this page:
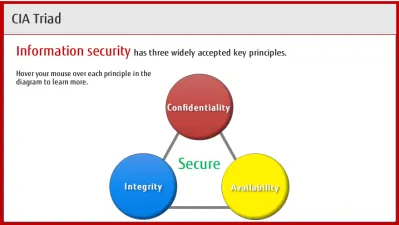 What is missing? Usability. Again, you can make a super secure system, but if it is extremely difficult to use, then there is a strong disincentive to use it.
What is missing? Usability. Again, you can make a super secure system, but if it is extremely difficult to use, then there is a strong disincentive to use it.
For example, in Windows one can control the access of every document down to exactly which users can read or update. But almost business user today ever uses it! It is too tedious. Sometimes, on a network drive, one might set the access to a complete folder to a group or something, but that leaves the door open for a wide variety of people. This is not really Microsoft’s fault: it is that the paradigm of setting up specific users access to specific files is just inherently tedious.
The most important aspect of a security system is that a regular business user can easily navigate the controls to accurately and easily restrict access from the right people, and allow access to the right people.
Part of a good usable system will be indicators that tell you when it is wrong and help you get around it. For example, when a user should have access, and doesn’t, there should be an easy way to request and get access — without a lot of tedium. The access control should be easily visible.
When there is a failure of security or a mis-configuration there should be a clear error message that accurately tells what was restricted and why. Most primitive security people believe that no error should be produced, or if one is, there should be no discernible information in it. All of this makes most data security environment so difficult to use that people avoid it.
But then I encounter this screen:
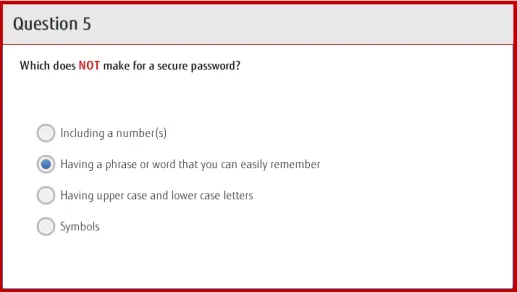 The checked answer is the one you must choose to get the question correcxt.
The checked answer is the one you must choose to get the question correcxt.
Here I thought the “security experts” had simply missed out on knowing that a password must be easy to remember, but they are actively against having passwords that are easy to remember! They actually believe that having a hard to remember password is better security! Unbelievable! When you have 30 to 40 password just for my job to remember, all of which are expected to be different (they aren’t I will tell you) and all of which are supposed to be hard to remember.
Again, an easily remembered password will not be written down, and therefor will be safer and more secure.
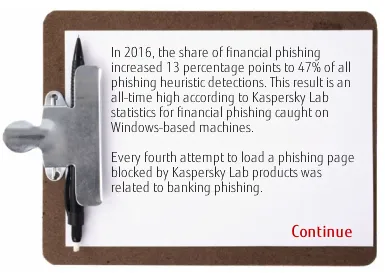 The course cites Kaspersky Lab while at the same time the US Department of Homeland Security is enacting a ban of all use of Kaspersky Labs products for security reasons.
The course cites Kaspersky Lab while at the same time the US Department of Homeland Security is enacting a ban of all use of Kaspersky Labs products for security reasons.
Another course
I got done with another course, and the last step of that course was to fill in a survey. I linked to the appropriate page, Logged in carefully. The instructions said to press a button to fill in the survey. This is what was presented to me:
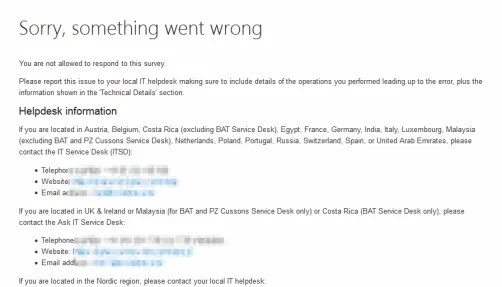 Is it access control gone wrong? Maybe. Probably. The people who made the survey probably have no idea this is happening. Because usability around access problems is not a priority, and in many cases it is strictly avoided.
Is it access control gone wrong? Maybe. Probably. The people who made the survey probably have no idea this is happening. Because usability around access problems is not a priority, and in many cases it is strictly avoided.