$13.5M Loss Shows Why Layered Fraud Defences Matter
Blog: Enterprise Decision Management Blog

Cosmos Bank in India recently had $13.5 million siphoned off by hackers linked to the Lazarus Group in North Korea. They exploited and succeeded in compromising two of the bank’s payment systems – the ATM Switch and the SWIFT payments system. The group is also alleged to have orchestrated the $81 million cyber heist at Bangladesh Bank by siphoning off SWIFT payments from the bank’s Federal Reserve account.
These attacks emphasize the need for layered fraud defences and controls that effectively mitigate such risks going forward. As the adage says: “There is no silver bullet!”
Layered Fraud Defences
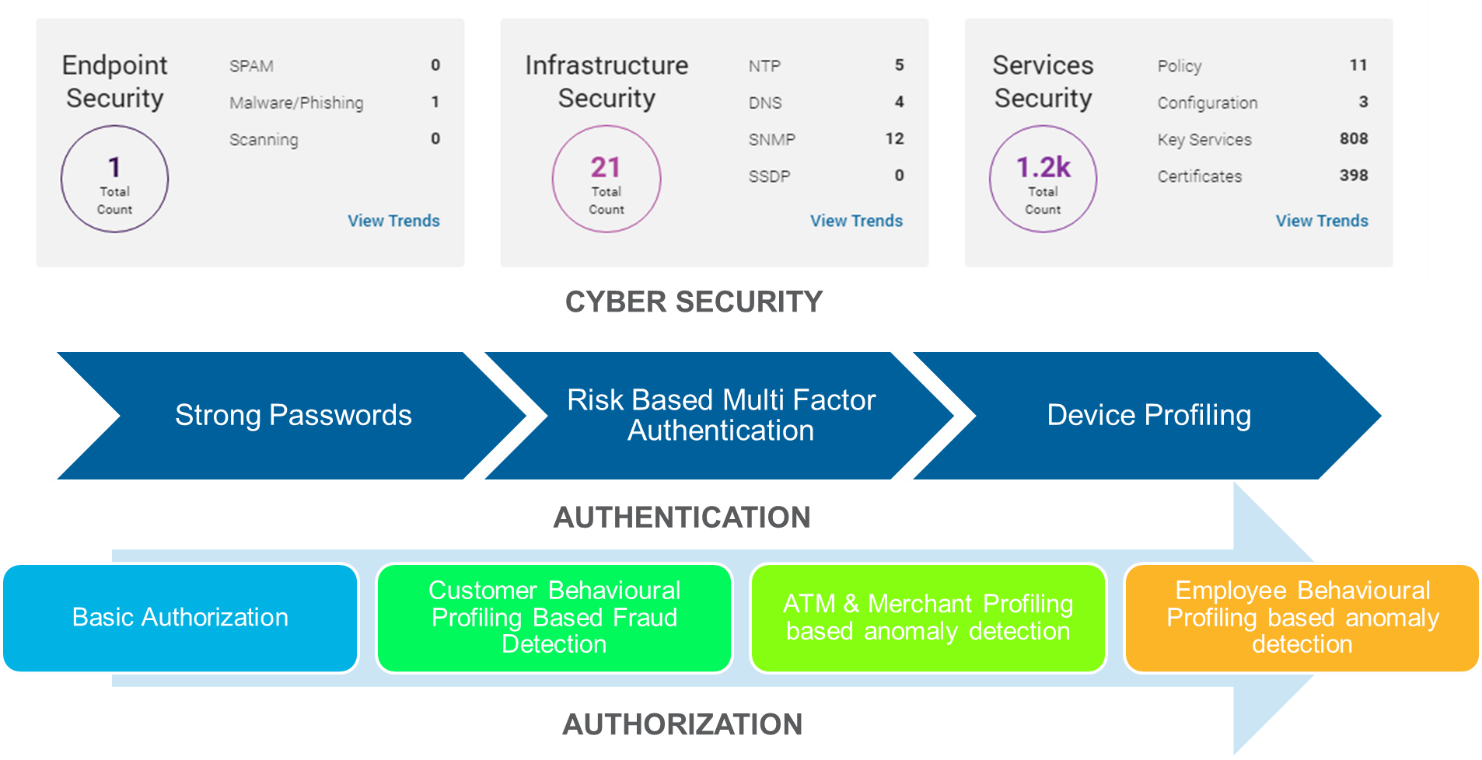
Layer 1 – Cybersecurity Measures
The layer for cybersecurity puts measures in place to monitor the security & internet infrastructure of the organization. Solutions for passive scanning (like the FICO® Cyber Risk Score) can check how strong or weak an organizations cybersecurity posture is. If there are vulnerabilities such as older versions of systems, outdated SSL certificates, use of poor network protocols, or the suspicion of phishing and malware originating from the organization’s servers, these are flagged and prompt corrective action can be taken.
However, cybersecurity should also cover active monitoring of the network by qualified network security personnel. Organizations need to have dedicated IT security resources who ensure that best practices are followed in every new business system implementation. This goes from something as basic as changing default admin passwords to more advanced activities like disabling unused ports and taking adequate measures to prevent SQL injection and cross-site scripting.
Layer 2 – Authentication
This layer covers password policies, two-factor and multi-factor authentication (MFA), device profiling, etc. It is noteworthy that Cosmos Bank’s back door was suspected to have been breached through a remote access to the system or through testing software. If remote access or test credentials are not required beyond a specific implementation or maintenance phase they should be disabled promptly.
Layer 3 – Authorization
Fraudsters don’t give up easily and will try to bypass strong cybersecurity and authentication controls using social engineering to dupe employees or working with insiders. To counter this, strong behavioural profiling and analytics-based authorization anomaly detection are needed – this isolates the riskiest of transactions and reduces noise so that legitimate customers are not unduly affected.
Payment Lifecycle Controls
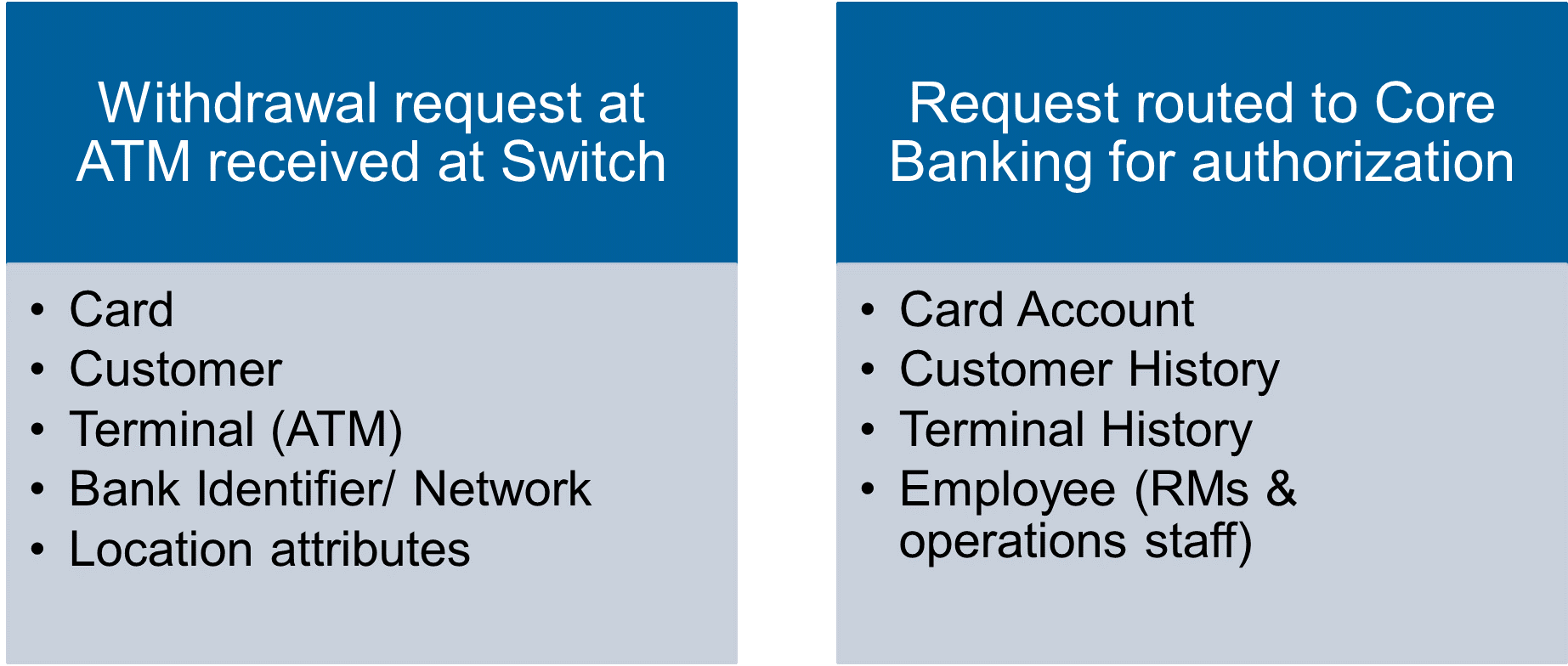
Payment transactions have a lifecycle and various entities are involved in each leg of the transaction.
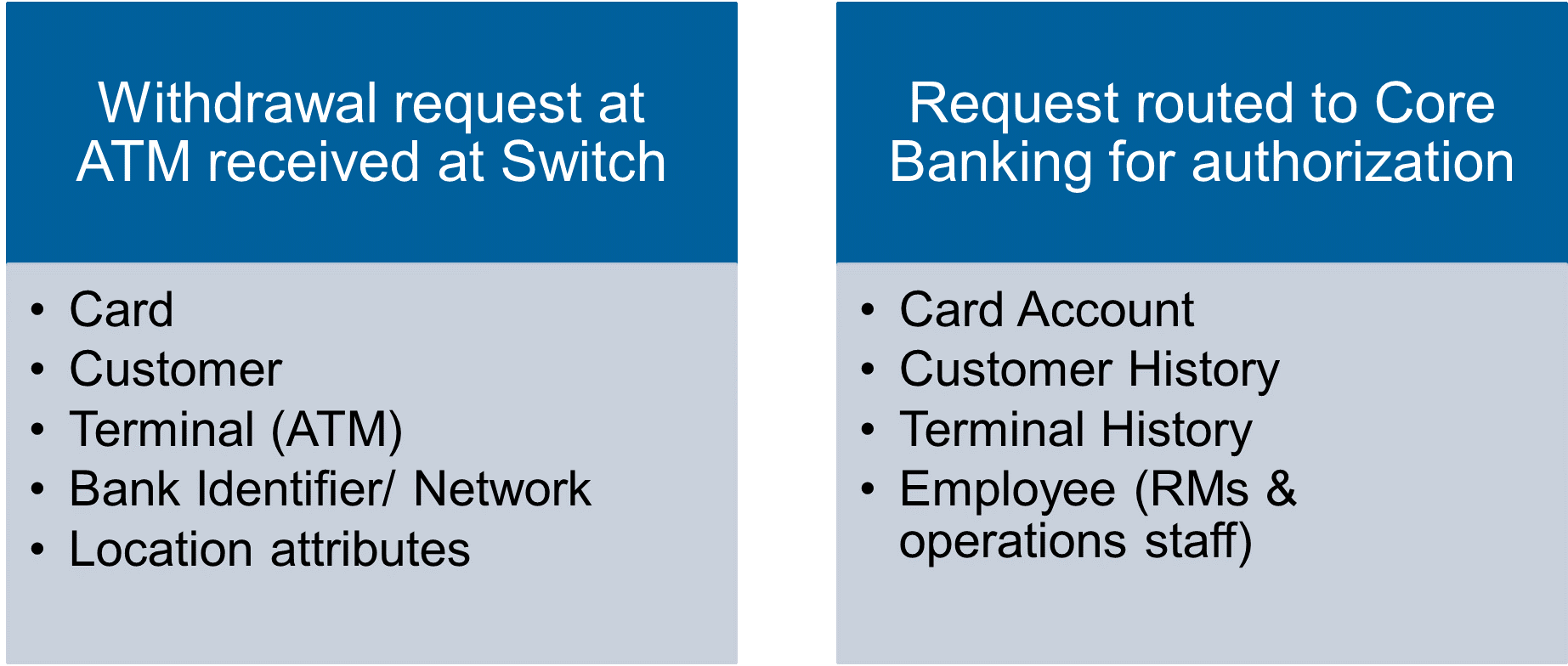
Several banks monitor transactions at multiple steps and have the capability to identify an “anomaly” on each jump of the transaction between bank systems.
Modern technology (like FICO® Falcon® Fraud Manager) uses artificial intelligence with profiling and machine learning algorithms combined with business rule writing capabilities to take real-time decisions on whether to allow specific payments. Workflow management capabilities are deployed after the real-time leg to provide a second intervention point to confirm the legitimacy of the transaction by either a fraud analysts or the customer.
Payment Lifecycle Controls
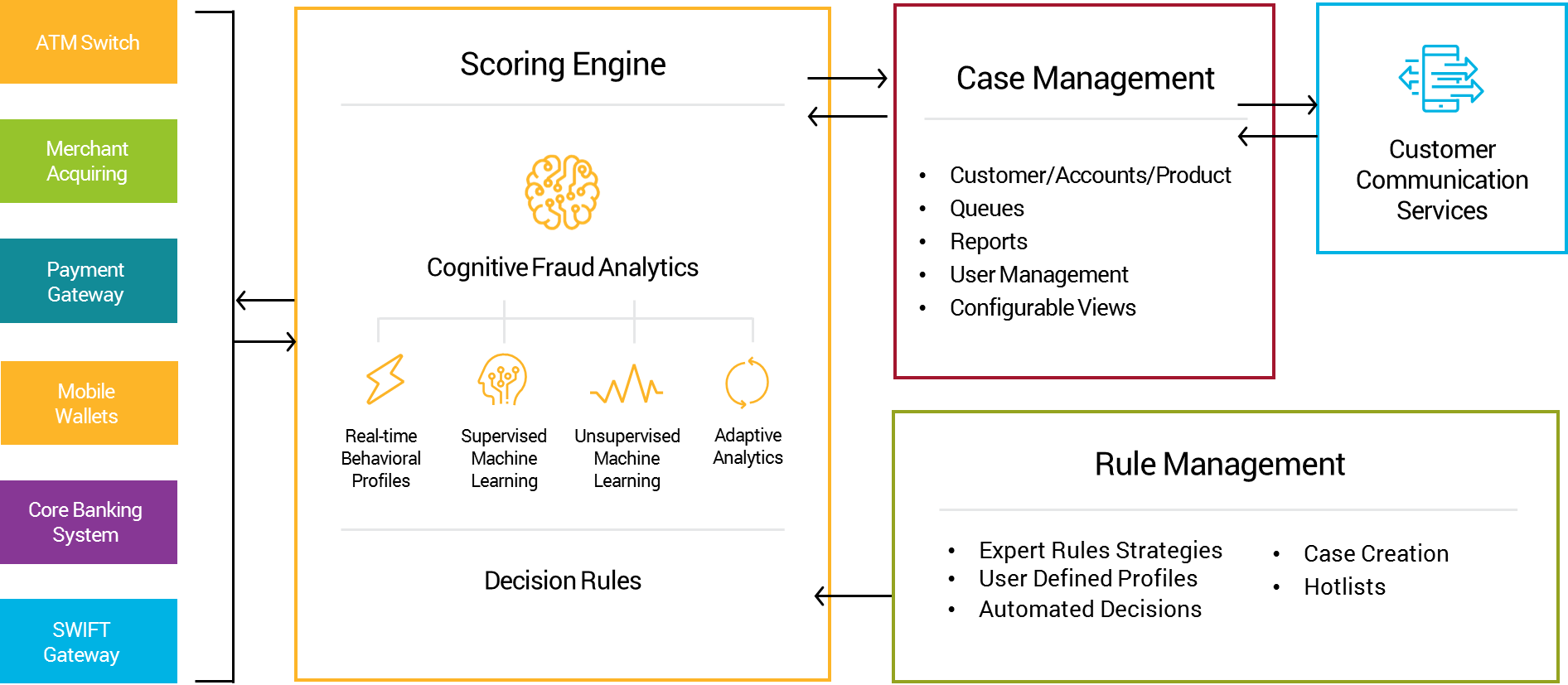
Real-time dynamic profiling tracks key transaction behaviors and patterns for each profiled entity to ensure easy recognition of uncharacteristic payments or activities. Profiles are updated in real time by every relevant event.
Profiles are not customer segments, clusters, nor a database of past transactions. They store multiple variables like favorite ATMs, countries, currencies, typical amounts, time of day and week when the customer typically uses his or her accounts, as well as other indicators of risk, such as prior address change or phone number change.
Multi-Entity Profiling
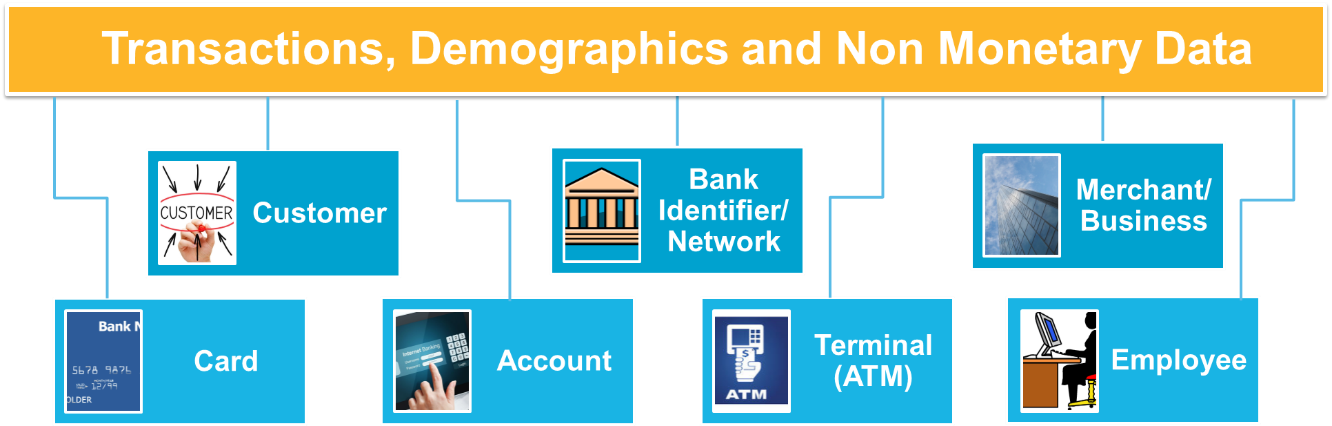
As illustrated above, profiling on multiple entities is done automatically by the system on transactional as well as non-financial data. Banks can detect anomalies in behavior across various entities to provide an early warning system of targeted attacks on the bank that have slipped through a point or channel-specific fraud check system. This is another way layered fraud defences can protect institutions.
The post $13.5M Loss Shows Why Layered Fraud Defences Matter appeared first on FICO.
Leave a Comment
You must be logged in to post a comment.








